Across BFSI, Healthcare, and SaaS: The Common Pattern Behind Cyberattacks
Cyberattacks are often explained through the lens of industries. Banking systems are targeted for financial gain, healthcare for sensitive patient records, and SaaS platforms for their scale and access into multiple organizations. This way of thinking feels logical, but it hides a deeper reality. When you analyse how real breaches happen, the industry becomes less relevant. What matters more is how modern systems are structured, connected, and trusted over time.
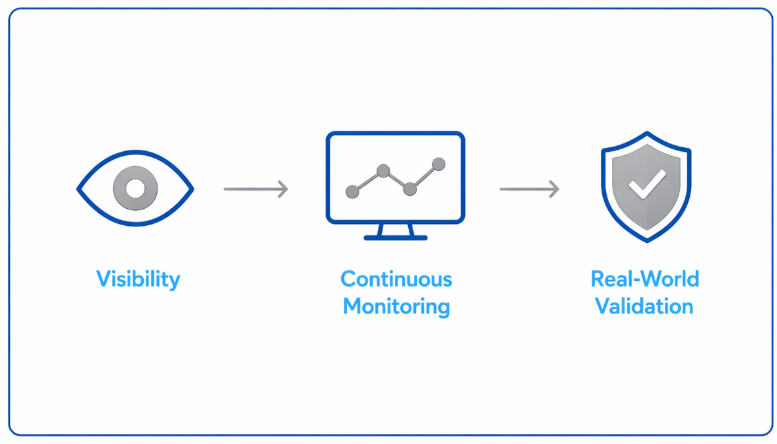
The truth is simple but uncomfortable. Cyberattacks fail because an organization belongs to BFSI, healthcare, or SaaS. They succeed because systems evolve in ways that increase reachability without increasing visibility. That pattern exists everywhere. Organizations today are moving toward continuous validation of real-world exposure rather than relying only on compliance frameworks.
Why Industry-Based Risk Is the Wrong Starting Point
Most organizations assess risk by comparing themselves to others in the same sector. A bank looks at financial threats, a hospital looks at data sensitivity, and a SaaS company focuses on platform security. While this helps in prioritizing compliance requirements, it creates a false sense of understanding. Attackers are not evaluating your industry classification. They are evaluating how your systems behave under access.
From an attacker’s perspective, your environment is not defined by what you do as a business. It is defined by what is connected, what is trusted, and what can be reached. This shift in perspective is where most security gaps begin.
What attackers look for includes:
Once you see risk this way, the industry label becomes secondary. The architecture becomes primary.
The Shared Architecture Across BFSI, Healthcare, and SaaS
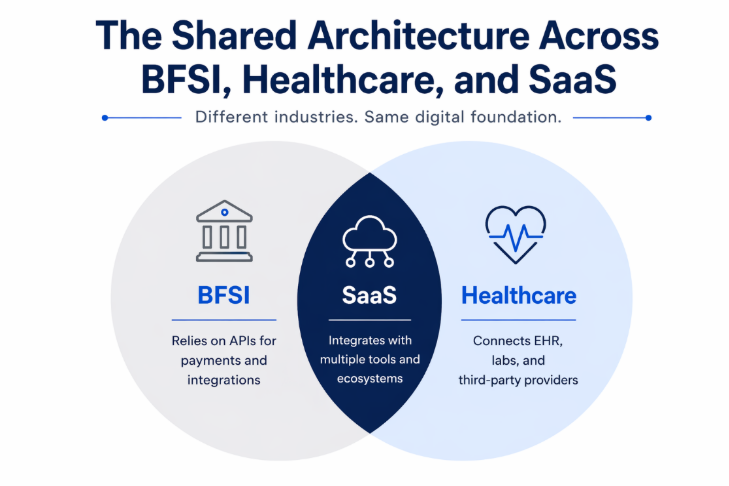
Despite operating in completely different domains, modern enterprises have converged into similar technology patterns. BFSI institutions rely heavily on APIs for payments and integrations. Healthcare systems connect electronic health records, labs, and third-party providers. SaaS platforms integrate with dozens of tools to deliver value to users. All of them operate in cloud-enabled, identity-driven environments. As environments become more interconnected, validating these relationships becomes critical. Explore how we assess real-world exposure
This creates a shared structure that includes:
This is not an industry-specific design. It is a modern digital architecture. And it creates the same type of exposure everywhere.
The Common Pattern Behind Real Cyberattacks
When you move beyond theory and look at actual breach scenarios, a repeating pattern becomes visible. It is not about a single vulnerability or a missing control. It is about how multiple correct systems interact in ways that were never fully validated.
This pattern typically unfolds in the following way:
Individually, each step feels normal and necessary. Collectively, they create a path.
Real-World Breaches That Follow the Same Pattern
To understand how this pattern plays out, it helps to look at real incidents. The industries differ, but the underlying mechanics remain consistent.
The SolarWinds attack is one of the most widely discussed examples. Attackers compromised a trusted software update mechanism, which then propagated across multiple organizations. The breach did not rely on breaking individual systems. It leveraged an existing trust relationship at scale.
In the Capital One data breach, the attacker exploited excessive permissions in a cloud environment. The infrastructure was functional, and controls existed, but access was broader than required. That gap enabled data exposure.
Similarly, the Moveout Transfer breach impacted organizations across industries by targeting a widely trusted file transfer system. Once again, the attack did not break trust. It moved through it.
These examples reinforce a critical point. Cyberattacks are not always about failure. They are often about unquestioned behaviour within working systems.
How Attack Paths Actually Form Inside Systems
To make this more practical, consider how a typical attack unfolds in a modern environment. It rarely starts with a dramatic system failure. Instead, it begins with something simple, like a compromised identity or a leaked credential. From there, the attacker does not need to break through layers of security. They move through what already exists.
A typical path looks like this:
At no stage is the system “broken” in the traditional sense. Everything works exactly as designed. The problem is that no one evaluated how far that access could extend when combined.
This is why modern breaches are often described differently. Attackers are not forcing their way in. They are navigating through the environment.
Why Compliance Does Not Address This Risk
Most organizations invest heavily in compliance frameworks, and rightly so. Standards like ISO 27001, regulatory requirements in BFSI, and healthcare data protection rules provide structure and governance. However, compliance validates whether controls exist and are documented. It does not validate how those controls behave together under real conditions.
This creates a gap between perceived security and actual exposure.
Compliance ensures:
But it does not answer:
As a result, an organization can be fully compliant and still be exposed in ways that are not immediately visible.
The Shift from Vulnerabilities to Reachability
Traditional security programs focus heavily on identifying vulnerabilities. This includes scanning systems, patching issues, and maintaining secure configurations. While this is important, it addresses only part of the problem. The more critical question is not whether vulnerabilities exist, but what can be reached if someone gains access.
Reachability becomes the defining factor of risk.
This includes:
This is where concepts like attack path analysis and exposure management become essential. They shift the focus from isolated weaknesses to interconnected risk.
What Needs to Change in Security Strategy
Addressing this pattern does not require abandoning existing controls or frameworks. It requires extending beyond them. Security needs to evolve from a static, control-focused approach to a dynamic, behaviour-driven model.
The shift involves rethinking how security is validated:
This is not a technical adjustment alone. It is a change in how organizations think about risk.
What This Means for Leadership and Decision-Makers
For leadership teams, especially CXOs and CISOs, this shift changes the nature of security conversations. The traditional questions around compliance and control coverage are no longer sufficient. What matters more is understanding the real-world impact of access and connectivity.
The conversation needs to move toward:
These are not theoretical questions. They directly define business risk, regulatory exposure, and operational resilience.
Final Perspective: The Pattern Already Exists
Cyberattacks are not random or isolated events. They follow patterns created modern systems are designed and operated. Integrations expand access, trust relationships extend reach, and data flows increase exposure. Over time, these elements combine into paths that are rarely visible but highly exploitable.
The most important realization is this. The pattern is not something external. It already exists within your environment.
The risk is not what is documented in policies or dashboards.
What Needs to Be Asked Now
Most organizations believe their risk is understood. Because controls are in place. Because audits are cleared. Because nothing has visibly failed. But leadership decisions are not meant to be based on what is visible. They are meant to be based on what is possible. So, the question is no longer about security posture. It is about exposure reality. Are your decisions being made on how your systems are designed or on how they behave today under pressure?
Because in modern environments, the gap between those two is where business risk truly lives.
Frequently Asked Questions
1. How do third-party integrations increase cybersecurity risk?
Third-party integrations expand access across systems. Even when properly configured, they introduce new trust relationships, API connections, and permissions that can be reused or misused. Over time, this creates hidden attack paths that are difficult to detect.
2. Are OAuth permissions and API integrations a security risk?
Yes, not because they are insecure by design, but because they are rarely reviewed after initial setup. OAuth tokens, scopes, and API access often remain active longer than needed, increasing the risk of unauthorized access through legitimate channels.
3. Why are most security tools unable to detect integration-based attacks?
Most tools focus on vulnerabilities, misconfigurations, or anomalies. Integration-based risks operate within allowed behaviour authenticated requests, valid tokens, and trusted services. Because everything appears normal, traditional security monitoring often misses these threats.
4. How can organizations reduce risks from SaaS and system integrations?
Organizations should move beyond static security checks and focus on:
.png)