Attack Surface vs Attack Path: Where Most Security Strategies Break in Practice
Why This Distinction Still Gets Ignored
Most organizations don’t lack security controls.
They lack clarity on how those controls behave once systems start interacting.
Security reviews usually begin with a familiar question:
That leads to asset inventories, vulnerability scans, and dashboards showing risk scores. From there, decisions are made, reports are shared, and confidence builds. But attackers don’t evaluate environments this way. They don’t stop at what is exposed. They focus on what becomes reachable after the first foothold. And that difference between exposure and reachability is where most security strategies quietly fail.
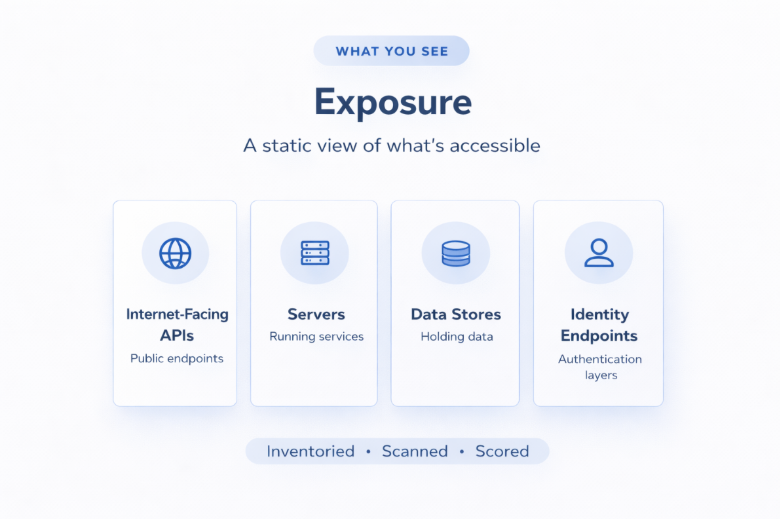
Understanding Exposure as a Static Layer
Attack surface is often treated as a measurable, controllable layer.
It includes everything externally visible or accessible:
Tools like vulnerability scanners, EASM platforms, and cloud security posture tools focus here.
They answer questions like:
This creates a snapshot. But it’s a static view. It does not reflect how those components behave when combined.
Where the Real Risk Forms: System Interactions

Attack paths emerge from relationships, not individual assets.
They are shaped by:
For example:
A public-facing API may only expose limited data.
But if that API uses a backend service account with broader permissions, and that account can query internal services or storage, the entry point becomes far more powerful than it appears. This is not a vulnerability in isolation. It’s a path created by design decisions.,
Real-World Example: How a “Low Risk” Issue Became a Breach
In multiple cloud breach cases (including misconfigured AWS environments), the initial issue was not a critical vulnerability.
It was something like:
Individually, these were classified as low or medium risk.
But attackers used them to:
Nothing in this chain was “critical” on its own.
But the path was.
This is the difference between:
Why Traditional Security Models Miss This
Most security programs are structured around control validation.
They check:
These are necessary. But they assume systems behave independently. Modern architectures don’t. Microservices, APIs, CI/CD pipelines, SaaS integrations everything is interconnected.
A CI/CD pipeline might:
If any one of these components is compromised, the pipeline itself becomes an attack path. But traditional security reviews rarely evaluate pipelines as attack chains. They evaluate each component separately.
The Role of Identity in Expanding Attack Paths
Identity is one of the most underestimated factors in attack paths. In cloud environments, identity often defines access more than network boundaries.
Common issues include:
For example:
A developer tool integrated via OAuth might have:
If compromised, that single integration can:
This is not an attack surface problem. It’s an identity-driven attack path.
Third-Party Integrations: The Silent Connectors
Every modern organization relies on third-party tools:
Each integration introduces:
Over time:
A third-party system with excessive access can act as a bridge between environments.
This is how attackers bypass well-secured perimeters. Not by breaking in directly. But by entering through something already trusted.
Why “Attack Surface Reduction” Doesn’t Solve This
Reducing exposed assets is still important. But it does not eliminate internal paths.
An environment can have:
And still be vulnerable internally.
Because once access is gained, internal trust often accelerates movement.
This is especially true in:
Attack surface reduction limits entry points. Attack path analysis determines impact.
How Attack Paths Change Over Time
One of the biggest challenges is that attack paths are not static. They evolve as the environment changes.
Every time you:
You potentially create new paths.
But most organizations don’t reassess risk at this level continuously. They rely on periodic audits.
Which means:
The system you validated three months ago is not the system you are running today.
What Mature Security Teams Do Differently
Organizations that move beyond this gap start treating security as a system behaviour problem, not a checklist.
They focus on:
1. Reachability Mapping
Understanding how far access can propagate from a single-entry point.
2. Privilege Path Analysis
Evaluating how identities can escalate privileges across services.
3. Continuous Validation
Not just scanning for vulnerabilities but testing how systems behave under attack scenarios.
4. Segmentation and Trust Boundaries
Reducing implicit trust between services and enforcing strict boundaries.
5. Integration Risk Reviews
Treating third-party connections as part of the attack surface, not external to it.
Where Penetration Testing Fits In
This is where practical testing becomes critical. Because tools can identify exposures. But only testing can validate behaviour. A well-executed penetration test does not just list vulnerabilities.
It answers:
It simulates what attackers do. Which is follow the path.
Reframing Cyber Risk for Leadership
At a leadership level, the conversation needs to shift.
From:
“Are we secure?”
To:
“If someone gets in, what happens next?”
Because that defines business risk.
Not the number of vulnerabilities.
Not the number of controls.
But the distance between entry and impact.
Closing Perspective
Most environments today are not insecure because they lack controls.
They are exposed because those controls were never evaluated together.
Attack surface gives you a list. Attack paths reveal reality. And in complex, interconnected systems, reality is rarely linear. It’s layered, connected, and constantly changing. The organizations that understand this don’t just reduce risk. They understand it.
From Visibility to Validation
Most organizations already have security controls in place.
The real gap is not implementation. It’s understanding how those controls behave when systems interact. Because in modern environments, risk is no longer about what exists. It’s about what becomes reachable.
If your team cannot clearly answer:
Then your security posture is still based on assumptions.
And assumptions are exactly where attackers operate.
👉 Start validating how your systems behave not just how they are designed.
Explore how your environment performs under real-world attack scenarios:
https://www.rexcybersolutions.com/
Frequently Asked Questions:
1: What is the difference between attack surface and attack path?
The attack surface refers to all the entry points that are exposed, such as APIs, servers, and applications.
An attack path, on the other hand, is the route an attacker takes after gaining initial access. It shows how different systems, permissions, and connections can be used together to reach sensitive data.
Understanding this difference is important because risk is not defined by exposure alone, but by how far access can extend.
2: Why is penetration testing important if we already use security tools?
Security tools help identify vulnerabilities and misconfigurations, but they don’t show how those issues can be combined in a real-world attack.
Penetration testing goes a step further by simulating attacker behaviour. It helps answer critical questions like whether access can be escalated, systems can be pivoted, or sensitive data can be reached.
This makes it essential for validating how security works in practice.
3: How do third-party integrations increase cybersecurity risk?
Third-party integrations often require API keys, access permissions, and data sharing between systems. Over time, these permissions can become broader and are rarely reviewed. If one of these external systems is compromised, it can act as a bridge into internal environments. This is why many modern attacks don’t break in directly they enter through trusted connections.
4: How can organizations identify real cyber risk instead of assumed risk?
Real cyber risk can only be understood by looking at how systems behave together, not just individually. This involves analysing access paths, validating permissions, and testing how far an attacker can move after initial entry.
Organizations that focus on reachability, attack paths, and continuous validation gain a much clearer picture of their actual risk.
.png)