Beyond Certification: Why ISO 27001 and DPDPA Compliance Don’t Reflect Your Actual Security Posture
When “Everything Looks Secure” Is the First Warning Sign
For most organizations, compliance feels like the finish line.
ISO 27001 certification is achieved. DPDPA requirements are implemented. Policies are documented, audits are cleared, and everything appears structured. On the surface, it creates a sense of control a belief that security is in place.
But reality often tells a different story.
Many organizations that are fully compliant still experience breaches, data exposure, and operational risk. Not because they ignored security, but because compliance does not always reflect how systems behave in real-world conditions.
That gap between what is documented and what happens is where risk quietly builds.
Compliance Proves Intent. It Doesn’t Prove Behaviour
Frameworks like ISO 27001 and regulations like DPDPA are critical. They bring discipline into how organizations manage data, define responsibilities, and establish controls.
They help answer structured questions:
But these frameworks operate at a design level.
They confirm that something exists, but not how everything behaves together in a live environment. Security failures rarely come from missing controls they emerge from how existing controls interact under real conditions.
Your System Didn’t Break. It Quietly Changed
Most environments don’t become risky overnight. They evolve.
New integrations are introduced. Access is extended. Systems start depending on each other. Data flows expand beyond original boundaries. Everything continues to function, and nothing raises concern.
But beneath that stability, something important shifts. Connectivity increases, trust expands across systems, and exposure grows without visibility.
Nothing looks broken. But the system is no longer what it was designed to be and that change is rarely reassessed.
Security Drift Happens Between Audits
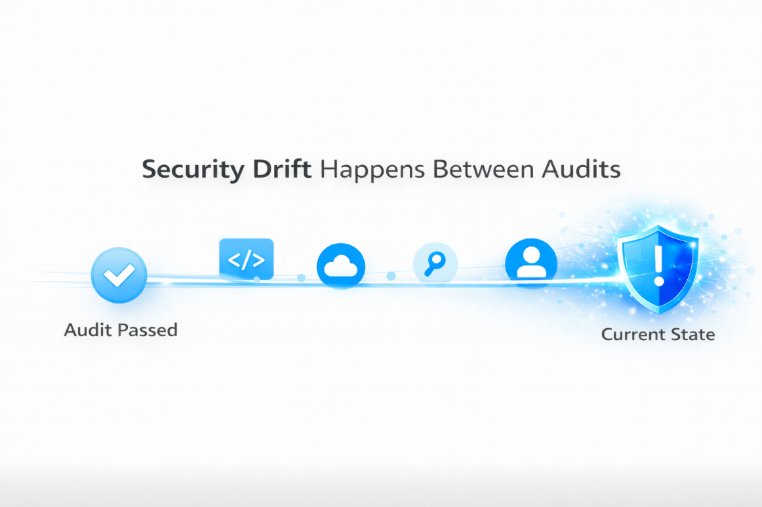
Compliance operates in intervals. Your environment does not.
Audits validate a moment in time, but your system evolves continuously. Every small operational decision contributes to that drift whether it’s a new API connection, a SaaS tool accessing internal data, a service account created for convenience, or temporary access that was never revoked.
Individually, these changes seem harmless. Collectively, they reshape your attack surface, and most organizations never validate these changes.
The Most Dangerous Risk Is Assumed Control
Organizations rarely lack controls. What they lack is validation.
Over time, assumptions replace verification. Permissions are trusted without review, systems rely on inherited access, integrations are assumed to be secure, and data exposure is not continuously monitored.
These decisions are made for efficiency. But together, they create hidden access paths, extended reachability, and uncontrolled trust relationships.
These risks don’t appear in documentation. They exist only in runtime behaviour.
ISO 27001 Tells You What Should Exist Not What Can Be Exploited
ISO 27001 is a powerful framework for building a structured security program. It ensures that risk management processes are defined, controls are implemented, and governance is maintained.
But it does not validate real-world exposure.
It does not answer:
ISO 27001 defines expectations. It does not validate attack paths and that distinction is where many organizations misjudge their security posture.
DPDPA Ensures Accountability. Attackers Look for Reachability
DPDPA shifts focus on responsible data handling. It emphasizes consent management, data protection obligations, and breach accountability.
But implementation alone is not enough.
The real challenge is operational consistency. Consent must be traceable across systems, access must align with defined policies, and data flows must be fully visible.
DPDPA defines legal responsibility.
Attackers don’t evaluate compliance they evaluate what is reachable.
Attackers Don’t Break Systems. They Follow Connections
Most modern breaches don’t come from isolated vulnerabilities. They emerge from connections.
A typical pattern unfolds quietly one system is trusted, that system connects to another, access extends beyond its original scope, and data flows across multiple environments.
Nothing fails. Everything works.
But internal systems become indirectly exposed, access paths extend across boundaries, and control assumptions no longer hold.
Attackers don’t need to break your system. They simply follow what is already connected.
A Real-World Pattern: When Compliance Passed, but Exposure Still Existed
In one real-world incident, a mid-sized technology organization was fully ISO 27001 certified and had implemented DPDPA-aligned data controls.
On paper, everything was correct. Risk assessments were completed, access policies were defined, integrations were approved, and audit evidence was clean.
The breach didn’t begin with a vulnerability. It began with a trusted integration.
A service account created years earlier quietly accumulated access as new systems were added. Nothing triggered alerts. No policy was violated. But the environment had changed.
When an attacker compromised a low-privileged account, they didn’t exploit a flaw. They followed existing trust.
That service account had:
Within hours, the attacker moved across systems using legitimate access paths.
No control failed.
No audit predicted it.
The organization was compliant but the system it was running was no longer the system it had assessed.
Why This Passed Audits but Failed in Reality
Every individual component met its requirement. The integration was approved, access was documented, policies existed, and reviews were completed.
What was missing was system-level validation.
No one asked:
The breach wasn’t caused by negligence. It was caused by assumed control.
Moving From Assumed Security to Proven Security
Preventing these scenarios doesn’t require abandoning compliance. It requires changing how security is validated.
Organizations already have controls. What they need is visibility into how those controls behave together.
That shift means:
Because security is not defined by what exists.
It is defined by what is reachable.
Final Thoughts
Compliance tells you that your system was designed correctly.
It doesn’t tell you what your system has become.
And in modern environments, that difference is everything.
Because breaches don’t happen when controls are missing.
They happen when systems evolve and no one notices what changed.
Security is no longer defined by what you implemented.
It is defined by what your systems allow today.
Frequently Asked Questions (FAQs)
1. Does ISO 27001 certification guarantee security?
No. ISO 27001 provides a structured framework for managing information security, but it does not guarantee that your systems are secure in real-world conditions. It validates that controls are defined and implemented, not that they work effectively together under evolving environments.
2. What is the difference between compliance and actual security posture?
Compliance focuses on documented controls, policies, and audit readiness.
Security posture reflects how your systems behave in real-time including access paths, integrations, and exposure.
An organization can be compliant and still have exploitable attack paths.
3. Why do breaches happen even in compliant organizations?
Most breaches don’t occur due to missing controls, but due to unvalidated connections and evolving environments.
As systems grow, integrations expand and access increases, creating new attack paths that are not reassessed after audits.
4. How does DPDPA compliance relate to cybersecurity risk?
DPDPA ensures lawful handling of personal data, but it primarily focuses on governance and accountability.
It does not continuously validate how data flows across systems or whether access paths can be exploited which is where real security risks emerge.
5. What is the best way to move from assumed security to proven security?
Organizations need to shift from periodic audits to continuous validation by:
.png)