Every New Integration Creates a New Attack Path: What Development Teams Often Miss
Introduction: This Usually Starts as “Just One More Integration”
Most integrations don’t feel like a big deal when they’re added. It’s usually something small.
“Let’s connect this API.”
“Let’s plug in this SaaS tool.”
“Let’s give this service access so things work faster.”
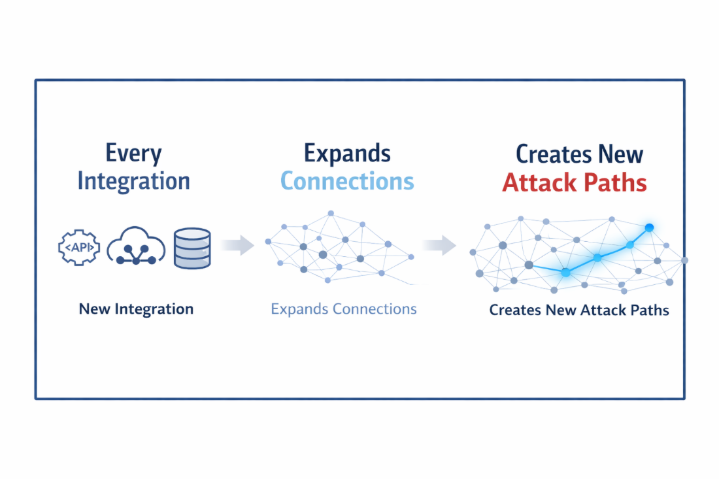
From a development perspective, it makes sense. You’re solving a problem, improving speed, shipping features. Nothing feels risky in that moment. But if you step back and look at it differently, something else is happening. Every time you connect one system to another, you’re not just enabling functionality. You’re creating a path. And most of the time, that path is never fully understood.
The Way We Think While Building
When you’re building systems, your focus is clear. Make it work. Make it fast. Make it reliable. Security is there, but usually in the background. You assume the access is fine, the permissions are reasonable, and the integration is safe because it’s needed. And to be fair, that assumption is what keeps things moving.
But here’s the part that gets missed.
What you are building is not just functionality. You are shaping how systems connect.
A Slight Shift in Thinking
Instead of asking, “Does this integration work?”, try asking, “If this integration is misused, what else can it reach?”
That question changes everything. Because suddenly an API is no longer just an endpoint, a token is no longer just access, and a connection is no longer just a feature. It becomes a possible path.
What Actually Happens When You Add an Integration
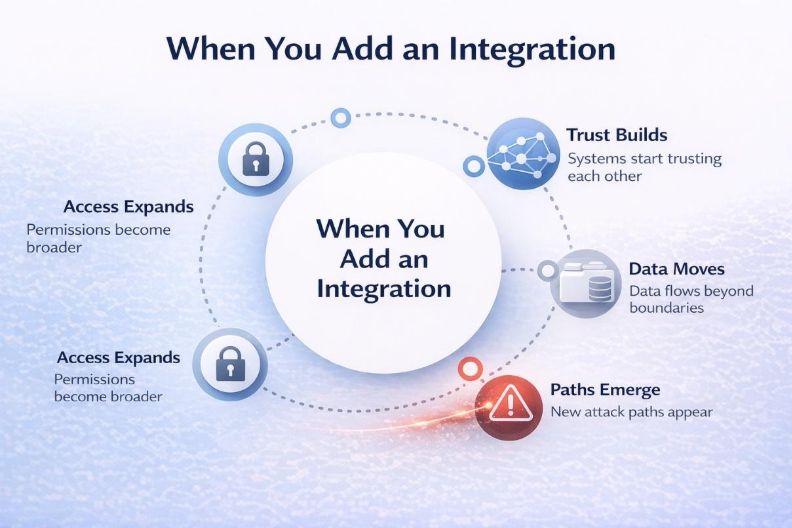
Most integrations follow the same pattern. You create access, usually through an API key, token, or service account. To avoid issues, permissions are often kept broader than necessary because it saves time and prevents friction.
Then systems start trusting each other. One service can call another, a vendor system can pull internal data, and a pipeline can access multiple environments. At first, everything is controlled. Over time, it becomes normal and no one revisits it.
At the same time, data starts flowing across more places than originally planned. Internal data reaches external tools, logs move into third-party systems, and dashboards pull from multiple sources.
Nothing looks broken. But something has changed. Your system is now more connected and more reachable than it was before.
Where Development Decisions Quietly Introduce Risk
This is not about mistakes. It’s about how systems evolve.
Most integrations are created during development or deployment, not during security review. Which means the risk is introduced at build time.
Not because something is wrong, but because permissions are slightly broader, access is not revisited, and connections are not mapped end to end.
Individually, each decision makes sense. Together, they create something no one planned a network of reachable paths.
The Gap Between Build Time and Reality
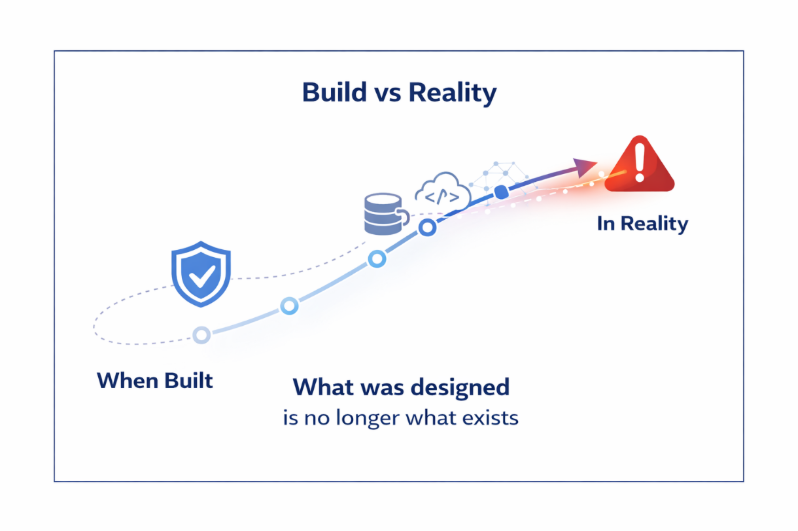
Once something is deployed, it becomes part of the system. Over time, more things get added. Another API, another vendor, another workflow.
But what was originally designed is no longer what exists. Connections increase, access expands, and data flows shift. Most of that change is not visible in one place, and it’s rarely re-evaluated from a risk perspective.
Let’s Make This Real
Imagine you integrate a third-party analytics tool and give it access to your cloud storage so it can generate reports. Everything works, the integration delivers value, and there are no issues.
Now fast forward. That analytics platform gets compromised. The attacker doesn’t need to attack your infrastructure directly. They already have a path.
They use the access you granted, move from the analytics platform into your storage, and access data that was never meant to be exposed externally. Because this activity comes from a trusted integration, it may not immediately raise suspicion.
Nothing was broken, but the path existed.
How Attackers Actually See Your System
Developers see systems as architecture. Attackers see systems as pathways. They don’t ask if something is secure. They ask where they can go from a given point. They start small, follow connections, move across trusted systems, and expand access step by step until they reach something valuable.
Integrations make this easier because they create those connections. In many cases, attackers don’t create attack paths. They discover the ones that already exist.
Why This Doesn’t Get Caught Easily
Most security checks happen at specific points like code reviews, scans, and audits. But integrations don’t stay static. They evolve.
What gets reviewed once is rarely reviewed again in context.
Most tools focus on individual components. They check if something is vulnerable, misconfigured, or outdated. But they don’t always show how everything is connected in real conditions.
And that is where the real exposure sits.
The Compliance Comfort Zone

There’s also a sense of confidence that comes from compliance. If systems pass audits, controls are in place, and policies are followed, things feel secure. But compliance validates what is documented. It doesn’t always reflect how systems behave after multiple integrations and changes. So, you can have everything correct on paper and still have exposure.
What Needs to Change in the Way We Build
This is not about slowing down development. It’s about adding awareness. When you create an integration, think beyond functionality. Think about reach, access, and what that connection enables. Because once something is connected, it becomes part of how your system behaves. And that behaviour is what attackers explore.
A Simple Way to Look at It
Every integration does two things. It solves a problem, and it creates a path. We focus heavily on the first. We rarely evaluate the second.
Final Thought

Integrations are necessary. They are what make modern systems work. But they also reshape your environment in ways that are easy to miss. They change how systems interact, expand what is reachable, and introduce connections that are rarely revalidated. Over time, those small changes add up.
The One Question That Matters
Next time you add an integration,
don’t just ask,
“Is it working?”
Ask,
“If this gets misused, what else becomes reachable?”
Because in modern systems, it’s not about what you build. It’s about what you connect. And that is where most risks go unnoticed.
Frequently Asked Questions (FAQs)
1. Why do integrations increase cybersecurity risk?
Every integration connects systems and expands access. Over time, these connections create new pathways that attackers can exploit, even if individual components appear secure.
2. What is an attack path in modern systems?
An attack path is the route an attacker uses to move across connected systems by leveraging access, permissions, and trust relationships between integrations.
3. How do APIs and third-party tools create hidden exposure?
APIs and third-party tools often require access to internal systems. If permissions are too broad or not regularly reviewed, they can unintentionally expose sensitive data and services.
4. Why is compliance not enough to ensure security?
Compliance validates policies and controls on paper, but it does not reflect how systems behave after multiple integrations and real-world changes, where hidden risks often exist.
5. How can organizations reduce risks from integrations?
Organizations should continuously review permissions, monitor system connections, validate security controls in real-world conditions, and regularly perform security testing like VAPT.
.png)