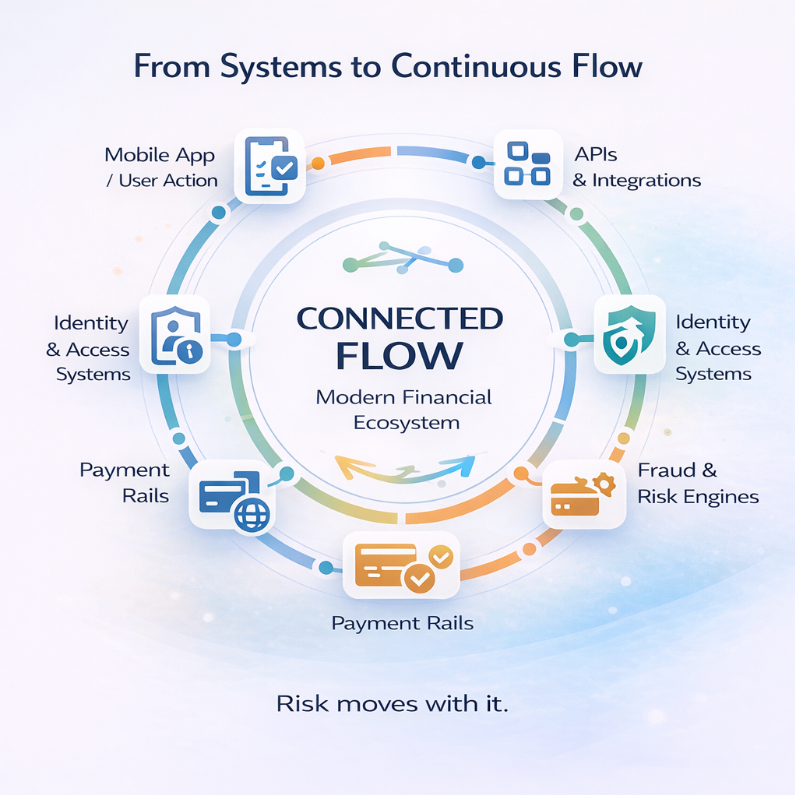
From APIs to Payment Rails: How Modern Cyberattacks Exploit Financial Ecosystems
1. The Financial Stack Isn’t a System Anymore-It’s a Flow
Financial systems used to be designed as controlled environments.
Core banking operated in isolation. Access was tightly managed. Transactions followed predictable paths. Security was about protecting a boundary. That boundary no longer exists. Today, financial operations function as continuous flows. A single customer action moves across mobile apps, APIs, identity systems, fraud engines, and payment networks all within seconds. Nothing pauses. Nothing isolates. And that changes the nature of risk. Because you’re no longer securing a system. You’re securing movement.
2. Every API Doesn’t Just Connect-It Extends Trust
APIs are often treated as technical connectors.
But every API is a decision about trust.
When one system calls another, it is implicitly trusted to:
Over time, these trust decisions accumulate. A fintech partner is given API access. An internal service is trusted across multiple environments. A vendor platform interacts with core systems. Individually, these feel controlled. But collectively, they create a network where trust travels far beyond its original intent.
And once trust becomes portable, so does risk.
3. Payment Rails Don’t Break-They Execute What They Trust
Payment systems are built for speed and reliability.
They are not designed to question intent. If a request is authenticated and correctly structured, it is processed. That is how modern payment rails operate. Which means the real risk is not whether payment systems can be breached. It is whether they can be misused. Once a request reaches the payment layer with sufficient trust, it is no longer a technical issue. It becomes financial impact.
4. The Real Attack Surface Is Not Your App, It’s the Relationships Between Systems
Security programs often focus on individual assets.
Applications.
Databases.
Endpoints.
But modern financial ecosystems don’t fail at the level of isolated components. They fail in the relationships between them. An API trusts another service. A payment system processes internal requests without deeper validation. A vendor integration operates with broader access than intended. None of these are vulnerabilities on their own. But together, they form pathways. And attackers don’t think in terms of systems. They think in terms of movement.
5. Where Financial Ecosystems Quietly Lose Control
Most organizations don’t make risky decisions intentionally. They make practical ones. Access is expanded slightly to avoid integration failures. Permissions are kept broad to reduce friction. Tokens are extended to prevent service interruptions. Over time, these decisions create exposure.
Third-Party Access as an Entry Point
A vendor system is integrated for onboarding or analytics. It becomes trusted. Monitoring is minimal because it is approved. If that vendor is compromised, the attacker doesn’t need to breach the bank.
They simply use the trusted connection.
Token Mismanagement Creates Persistent Access
API tokens and service accounts are often long-lived. They are reused across services and rarely rotated. This creates a condition where access becomes permanent. An attacker who gains access to one token can move across systems without raising suspicion.
API Chaining Builds Hidden Paths
One API connects to another. That service triggers additional systems. Data flows across multiple layers.
No single API appears risky. But together, they create paths no one explicitly designed and no one monitors.
6. Real Incident Patterns in Financial Cyberattacks
These risks are not theoretical. They follow consistent real-world patterns.
API Abuse in Fintech Integrations
In many fintech ecosystems, APIs are exposed to partners with broad permissions. Attackers exploit these APIs not by breaking them, but by using them in unintended ways extracting excess data or triggering backend processes.
Payment Fraud Through Trusted Systems
Instead of hacking payment infrastructure, attackers leverage trusted internal workflows. Once inside, they initiate transactions that appear legitimate because they follow expected formats.
Third-Party Compromise Leading to Banking Exposure
A compromised vendor system becomes a bridge into financial infrastructure. Because the connection is trusted, malicious activity blends with normal operations.
Token Reuse Across Environments
Credentials used across development, staging, and production environments allow attackers to move laterally once access is obtained.
These incidents don’t rely on sophisticated exploits.
They rely on understanding how systems interact.
7. How an Attacker Moves from API Access to Financial Impact
Modern cyberattacks are quiet and structured.
They typically follow a pattern:
At no stage does the system appear broken.
Because everything happening is allowed.
8. Why Most Security Programs Don’t See This Coming
Most organizations invest heavily in security.
They have:
But these approaches answer a limited question:
“Is everything configured correctly?”
They do not answer:
“What happens when everything works correctly, but in the wrong sequence?”
Compliance validates structure.
Tools monitor events.
But neither fully captures behaviour across interconnected systems.
And that is where modern cyberattacks operate.
9. The Visibility Gap: What You Can’t See Is What Gets Exploited
The biggest gap in financial cybersecurity is visibility.
Most organizations cannot clearly answer:
Without these answers, security becomes assumption driven.
And assumptions create blind spots.
In highly connected environments, blind spots are where attackers operate.
10. Why This Risk Is Increasing in 2026
This problem is not static. It is accelerating.
Open Banking Expansion
Financial institutions are exposing more APIs to external partners, increasing the number of trust relationships.
API-First Fintech Growth
New services are built around APIs from day one, often prioritizing speed over strict access control.
Real-Time Payment Systems
Instant payment platforms reduce the time available to detect and stop malicious activity.
Third-Party Dependency Growth
Organizations rely on multiple vendors for critical functions, expanding the attack surface indirectly. As connectivity increases, so does reachability and reachability defines risk.
11. Rethinking Cyber Risk in Financial Systems
Cyber risk needs to be reframed.
Not as a question of protection.
But as a question of behaviour.
Instead of asking:
“Are our APIs secure?”
Ask:
“If this API is misused, what else becomes reachable?”
Instead of asking:
“Are payment systems protected?”
Ask:
“What happens if a trusted request is malicious?”
Because modern risk is not about entry.
It is about movement.
12. Testing the System You Actually Run Not the One You Designed
Architectures are designed with intent.
But systems evolve over time.
Integrations expand. Access grows. Dependencies increase.
The system you operate is not the one you originally secured.
Which is why validation matters.
Not checklist-based testing.
But behaviour-driven testing.
A meaningful penetration test answers:
It reveals how the system behaves not how it is supposed to behave.
13. The One Question That Defines Financial Risk
At a leadership level, cybersecurity is often simplified.
Are we secure?
Are we compliant?
But these questions don’t define risk.
The real question is:
how far can they move before it impacts money?
Because in financial ecosystems, impact is immediate. And often irreversible.
Final Reflection
Modern financial ecosystems are built for connectivity. Apis extend trust. Payment systems execute that trust. And attackers follow that path. Nothing needs to break. Everything just needs to work in the wrong way. And that is what makes modern cyberattacks so difficult to detect. Not because they are complex.
But because they align perfectly with how systems already behave.
FREQUENTLY ASKED QUESTIONS
1. How do cyberattacks happen in banking systems today?
Modern cyberattacks in banking don’t usually start with system breaches. They begin by exploiting APIs, third-party integrations, or misused credentials, allowing attackers to move across connected systems without detection.
2. Why are APIs considered a major cybersecurity risk in financial services?
APIs expose critical data and functions. If they are over-permissioned or poorly monitored, attackers can use them to access multiple systems, extract sensitive data, or trigger financial transactions.
3. What is the biggest cybersecurity risk in fintech and digital banking?
The biggest risk is not vulnerabilities, but uncontrolled connectivity where multiple systems trust each other, creating hidden attack paths across APIs, vendors, and payment systems.
4. How do attackers exploit payment systems without breaking them?
Attackers don’t need to hack payment systems directly. They use trusted access to initiate legitimate-looking transactions, manipulate workflows, or redirect funds through existing payment rails.
5. Why is third-party access a major risk in BFSI cybersecurity?
Third-party vendors often have broad access to internal systems. If a vendor is compromised, attackers can use that trusted connection to enter the financial ecosystem without triggering alerts.
.png)