From Factory Floor to Cloud: How Cyberattacks Travel Across Industrial Systems
Introduction: The Illusion of Isolation

For a long time, industrial systems were considered safe simply because they were isolated.
Factory floors ran on proprietary networks. Machines spoke their own protocols. IT and OT environments operated in parallel worlds that rarely intersected. That assumption no longer holds.
Today, production lines connect to cloud dashboards. Maintenance teams access systems remotely. Vendors integrate directly into operational environments. Data flows continuously between machines, applications, and external platforms. What was once isolated is now deeply interconnected. And in that shift, something fundamental has changed:
Cyberattacks no longer stay in one place.
They move. They travel. They follow the path of connectivity.
The Modern Industrial Stack Is No Longer Linear
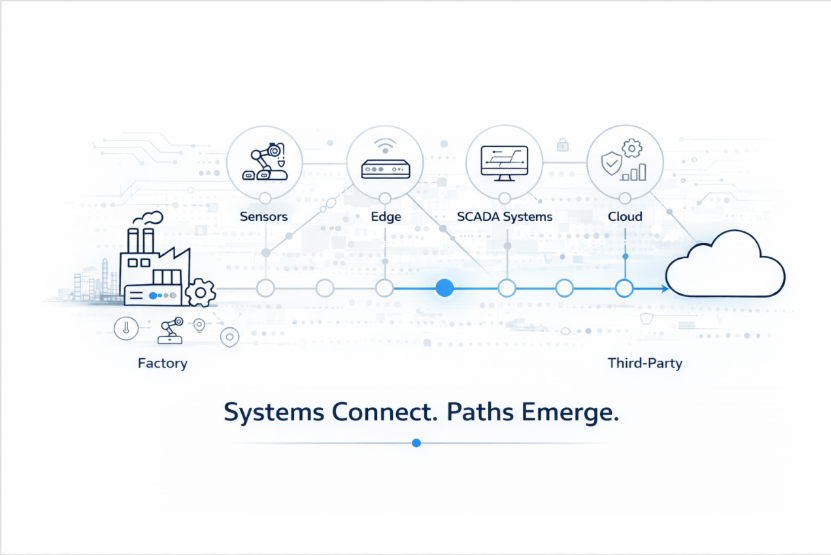
Industrial environments are no longer just machines and controllers.
They are ecosystems.
A typical setup today includes:
Each layer adds value. Each connection improves efficiency. But each connection also creates a pathway.
And attackers don’t think in layers. They think in paths.
Where the Journey Begins: The Entry Point
Most cyberattacks don’t start with something dramatic.
They start quietly.
A compromised vendor credential.
A misconfigured remote access port.
An exposed API used for system integration.
Nothing looks broken.
Everything is functioning exactly as designed. That’s what makes it dangerous. Because the system is not failing.
It is behaving in a way that allows movement.
The Real Risk: Movement, Not Entry
Security conversations often focus on preventing entry.
Firewalls. Endpoint protection. Access controls.
But modern attacks are not defined by how they get in.
They are defined by how far they can go once inside.
In industrial environments, that movement is often easier than expected.
Why?
Because systems are built to trust each other.
These trust relationships are necessary for operations.
But they are rarely revisited.
And over time, they expand.
From OT to IT to Cloud: The Attack Path
Let’s break this down in a real-world flow.
An attacker gains access to a low-level system on the factory floor.
From there:
What started as a small foothold becomes a pathway to critical systems. Not because of a single failure.
But because everything is connected.
Why Traditional Security Models Fall Short
Most organizations invest heavily in security controls.
They have:
These are necessary.
But they answer a limited question:
“Is everything configured correctly?”
They do not answer:
“What happens when everything works correctly, but in sequence?”
Because cyberattacks are not isolated events. They are sequences of actions. And most security models are not designed to evaluate sequences.
The Hidden Complexity of Industrial Integrations
Industrial environments evolve constantly.
New systems are added to improve efficiency.
New vendors are onboarded to support operations.
New data flows are created for visibility.
Each integration is justified.
Each change is small.
But collectively, they reshape the environment.
Over time, the system becomes:
And that shift is rarely documented in a way that reflects reality.
The Cloud Amplifies Everything
Cloud platforms play a critical role in modern industrial systems.
They enable:
But they also amplify risk.
Because the cloud is not just another layer.
It is a multiplier of connectivity.
Once data reaches the cloud, it often becomes accessible to:
And if access is not tightly controlled and continuously validated, the cloud becomes a bridge.
A bridge between internal systems and external exposure.
Why Compliance Is Not Enough
Many organizations rely on compliance frameworks to validate their security posture.
They pass audits.
They implement required controls.
They document policies and processes.
And for a moment, everything feels secure. But compliance validates what is documented. It does not always reflect how systems behave after multiple integrations and changes.
You can have:
And still have exposure.
Because compliance focuses on structure.
Cyber risk emerges from behaviour.
The Blind Spot: Inter-System Behaviour
This is where most organizations struggle.
They understand individual systems.
They secure individual components.
But they don’t fully understand how systems behave together.
Questions that often go unanswered:
These are not configuration questions.
They are behavioural questions.
And they define real risk.
What Attackers Actually Do
Attackers don’t break systems randomly.
They observe. They map relationships. They follow the path of least resistance.
They look for:
And then they move. Step by step. System to system. Layer to layer.
Until they reach something valuable.
Reframing Industrial Cyber Risk
At a leadership level, the conversation needs to shift.
From:
“Are our systems secure?”
To:
“If someone gets in, what can they reach?”
Because that defines business impact. Not the number of vulnerabilities. Not the number of controls.
But the distance between entry and critical systems.
Where Security Needs to Evolve
To address this reality, organizations need to rethink how they validate security. This doesn’t mean abandoning existing controls. It means extending beyond them.
Key shifts include:
1. From Configuration to Behaviour
Understanding not just how systems are set up, but how they interact in real scenarios.
2. From Assets to Relationships
Mapping trust relationships between systems, not just individual assets.
3. From Prevention to Visibility
Focusing on what is reachable, not just what is protected.
4. From Static to Continuous Validation
Recognizing that environments change constantly, and security must adapt accordingly.
The Role of Real-World Testing
This is where practical validation becomes critical. Because tools can identify exposures. But only testing can validate behaviour. A well-executed security assessment doesn’t just list vulnerabilities.
It answers:
It simulates how an attacker would move. And that is where real insight comes from.
Final Thoughts: Cyberattacks Follow Connectivity
Industrial systems were never designed for this level of connectivity. But that is the reality today. Factory floors connect to cloud platforms. Operational systems integrate with external tools. Data flows across environments continuously. And cyberattacks follow those connections. They don’t need to break everything. They just need to find a path.
Because in modern industrial environments,
risk is no longer defined by what exists.
It is defined by what is reachable.
Frequently Asked Questions
1. How do cyberattacks move from factory systems to the cloud?
Cyberattacks typically start from a weak entry point such as a compromised device, vendor access, or exposed API. From there, attackers move through connected systems edge devices, central servers, and eventually cloud platforms by exploiting trust relationships and integrations between systems.
2. Why are industrial systems (OT environments) vulnerable to cyberattacks today?
Industrial systems were originally designed for isolation, not connectivity. With the rise of cloud integration, remote access, and third-party tools, these systems are now interconnected. This increased connectivity creates multiple pathways that attackers can use to move across environments.
3. What is the biggest cybersecurity risk in modern industrial environments?
The biggest risk is not just unauthorized access, but how far an attacker can move once inside. Poorly managed trust relationships, over-permissioned access, and unmonitored integrations allow attackers to travel across systems and reach critical assets.
4. How is cloud connectivity increasing cyber risk in manufacturing?
Cloud platforms centralize data and connect multiple systems, users, and applications. If access controls are not tightly managed, the cloud can act as a bridge between internal industrial systems and external exposure, significantly increasing the attack surface.
5. Is compliance enough to secure industrial systems?
No. Compliance ensures that security controls and policies are in place, but it does not guarantee that systems are secure in real-world scenarios. Cyber risks often arise from how systems interact and behave together, which compliance frameworks do not fully validate.
.png)