How Do You Verify Your Web Application Is Secure When Every API and Integration Expands What Can Be Reached?

Most organizations today don’t question whether they have security in place.
They have tools, controls, frameworks, and processes. They run scans, fix vulnerabilities, and pass audits. On the surface, everything looks structured and under control. But the real question is not whether security exists. It is whether that security still holds when your web application behaves the way it does in the real world. Because modern web applications are no longer isolated systems.
They are ecosystems built on APIs, connected to third-party services, integrated with internal platforms, and accessed by users, vendors, and automated processes across different environments. And with every new connection, something changes. Not visibly. Not immediately. But structurally. Access expands.
The Problem Isn’t Vulnerabilities. It’s Reachability.
Most security programs are designed to answer a straightforward question:
“Are there vulnerabilities in the application?”
And they do this well. Vulnerability scanners, SAST, DAST, and code reviews can identify issues like injection flaws, misconfigurations, or outdated libraries.
But this approach assumes something important:
That vulnerabilities are the primary driver of risk. That’s only part of the picture.
Because what matters more is:
This is where most organizations lose visibility.
A vulnerability in isolation may seem low risk.
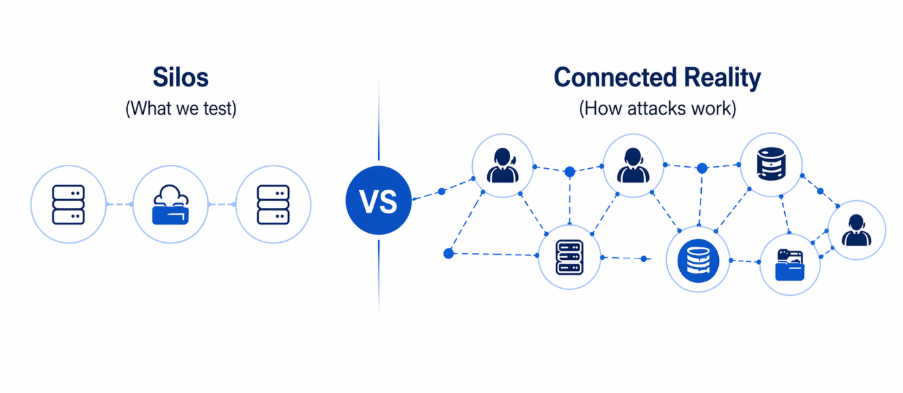
But when combined with API access, authentication flows, or internal integrations, it can create a path to something far more critical. This is not a flaw in tools. It’s a limitation of perspective. Security is still being evaluated at the level of individual components, while attacks operate across systems.
What Modern Web Applications Actually Behave
To understand why verification is difficult, it helps to look at how web applications evolve over time.
A typical application might start with a simple architecture:
Security is implemented around these components. Access is controlled. Everything is predictable.
But growth introduces change.
New features require new APIs.
Integrations bring in third-party services.
Authentication expands to include SSO, OAuth, and external identity providers.
Background jobs and pipelines start interacting with multiple systems.
Over time, the application becomes:
None of this is inherently insecure.
In fact, it is necessary for scale and functionality.
But it introduces a different kind of risk.
Not visible breakpoints.
But invisible pathways.
The Hidden Complexity of APIs and Integrations
APIs are the backbone of modern web applications. They enable communication between systems, automate workflows, and extend functionality. But they also introduce a challenge: Apis don’t just expose functionality. They expose access.
And that access is often broader than intended.
Common patterns include:
Each of these may seem minor individually.
But together, they create a network of reachable paths.
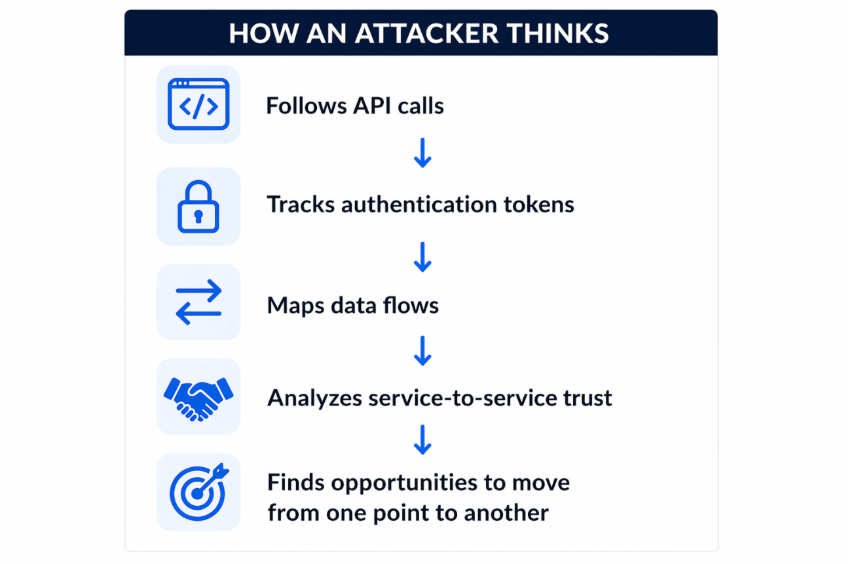
An attacker does not need to break the system. They need to understand it.
They follow:
And they look for opportunities to move from one point to another. This is not about exploiting a single flaw. It’s about navigating the system.
Why Traditional Testing Falls Short
Most organizations perform some form of testing:
These are important. But they often operate within defined boundaries.
They answer questions like:
What they often don’t answer is:
This is where the gap exists.
Because real-world attacks don’t respect testing boundaries. They don’t stop at one system. They don’t follow predefined scopes. They follow what is reachable.
The Shift from Testing to Verification
Verifying web application security requires a different approach. Not just identifying issues but understanding behaviour.
It means asking:
This is where penetration testing, when done correctly, becomes critical. Not as a checklist activity. But to simulate how your application behaves under real-world conditions.
What Effective Web Application Penetration Testing Should Actually Do
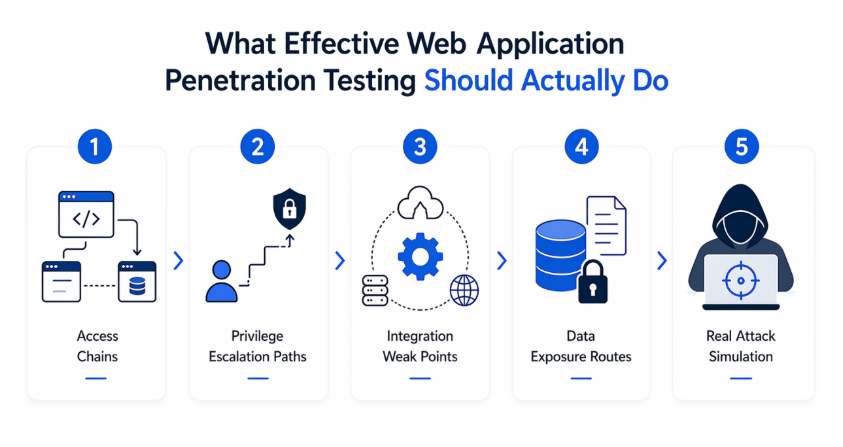
A meaningful penetration test goes beyond identifying vulnerabilities.
It explores:
1. Access Chains
Instead of testing endpoints in isolation, it evaluates how access flows across the application.
Can one API call lead to another?
Can tokens be reused or escalated?
Can internal services be reached indirectly?
2. Privilege Escalation Paths
It examines whether limited access can be expanded.
Can a normal user gain admin-level capabilities?
Can service accounts be abused?
Can role boundaries be bypassed?
3. Integration Weak Points
It tests how third-party and internal integrations behave.
Are external services trusted too much?
Do integrations expose sensitive data?
Can attackers move between systems through these connections?
4. Data Exposure Routes
It looks at how data flows through the application.
Is sensitive data accessible through unexpected endpoints?
Are responses over-sharing information?
Can data be aggregated from multiple sources?
5. Real Attack Simulation
Most importantly, it mirrors attacker behavior.
It does not stop at finding a vulnerability.
It asks:
“What does this enable?”
Because that is what defines risk.
Why This Matters for Leadership
For leadership teams, this is not a technical nuance. It is a business concern.
A web application is often the entry point to:
If access can be extended beyond intended boundaries, the impact is not limited to the application itself.
It affects:
This changes the nature of security discussions.
From:
“Are we secure?”
To:
“If someone gets in, what can they reach?”
Because that determines real-world risk.
From Assumed Security to Proven Security
Most organizations don’t ignore security. They invest in it, implement controls, and follow frameworks.
But over time, systems evolve.
And security assumptions are rarely revisited at the same pace. This creates a gap. Not because controls are missing. But because behaviour is untested. Verifying security posture means closing that gap.
It means moving from:
Final Thought
Your web application is not defined by its architecture diagrams, its security tools, or its compliance reports.
It is defined by how it behaves when everything is connected.
Because in modern environments, nothing is truly isolated.
Every API call, every integration, and every access decision shape what is possible.
And what is possible is what attackers will find.
“Is your web application secure?”
“Have you verified what it allows?”
Frequently Asked Questions
1. How can I verify if my web application is truly secure?
Verifying web application security goes beyond running vulnerability scans or passing audits. It requires understanding how your application behaves in real-world scenarios how APIs interact, how access flows across systems, and whether attackers can move beyond initial entry points. This is typically achieved through penetration testing and continuous validation, where security is tested based on what is reachable, not just what is configured.
2. What is the difference between web application security testing and penetration testing?
Web application security testing often focuses on identifying known vulnerabilities using automated tools or predefined checks. Penetration testing goes deeper. It simulates real attacker behaviour to determine how vulnerabilities can be exploited, chained, and used to access sensitive systems or data. In short, testing finds issues penetration testing validates impact.
3. Why do web applications get compromised even after passing security audits?
Security audits and compliance checks validate whether controls are implemented correctly. However, they do not always reflect how systems behave after multiple integrations, API expansions, and access changes. Over time, these changes create new access paths and trust relationships that are rarely re-evaluated, allowing attackers to exploit what is reachable even if everything looks secure on paper.
4. How do APIs and integrations increase security risk in web applications?
APIs and integrations expand functionality, but they also expand access. Poorly managed API tokens, excessive permissions, inconsistent authorization checks, and trust between services can create unintended pathways. Attackers often exploit these connections to move across systems, access sensitive data, or escalate privileges without triggering traditional security controls.
5. How often should web application penetration testing be performed?
Penetration testing should not be a one-time or annual activity. It should be performed:
Because web applications evolve constantly, testing must keep pace with those changes to ensure that new access paths do not introduce unseen risks.
.png)