Operationalising DPDPA with ISO 27001: A Practical Compliance Roadmap for CISOs

Most organizations believe they know where their personal data resides.
In reality, very few can clearly demonstrate how that data is governed, protected, and monitored across their systems.
With the introduction of India’s Digital Personal Data Protection Act (DPDPA), organizations are now expected to prove accountability for how personal data is collected, processed, stored, and secured.
For CISOs and security leaders, the challenge is not simply understanding the regulation it is operationalising DPDPA compliance across complex IT environments, cloud platforms, and third-party ecosystems.
This is where ISO 27001 provides a structured and practical framework. By integrating DPDPA requirements into an Information Security Management System (ISMS) and applying the Plan–Do–Check–Act (PDCA) model, organizations can translate regulatory expectations into operational security practices.
This article outlines a practical roadmap for CISOs to operationalise DPDPA using ISO 27001, covering data mapping, risk management, consent governance, and continuous compliance monitoring.
Why Operationalising DPDPA Is Challenging for Organizations:
Many organizations believe they know where personal data exists. They know the primary application and the central database.
However, in modern digital environments, personal data rarely remains confined to a single system. It often spreads across multiple platforms and services, including:
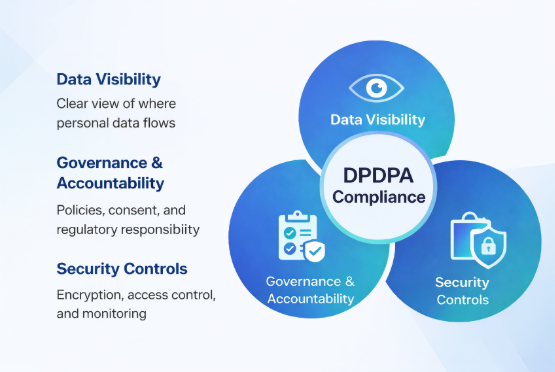
Without strong governance and visibility, it becomes difficult to track how personal data is processed, accessed, and protected. This is why many organizations struggle when regulators ask them to demonstrate accountability and data traceability. DPDPA compliance therefore requires more than policies. It requires structured operational controls, visibility, and continuous monitoring.
How ISO 27001 Helps Operationalise DPDPA:
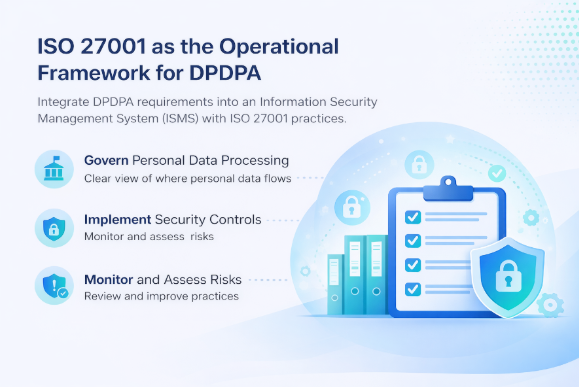
ISO 27001 provides a globally recognized framework for managing information security through an Information Security Management System (ISMS). Instead of treating DPDPA as a separate legal requirement, organizations can integrate data protection into their existing security governance framework.
By aligning ISO 27001 controls with DPDPA obligations, CISOs can:
This approach transforms compliance from a one-time legal exercise into a continuous operational program.
A Practical Roadmap for CISOs: DPDPA Implementation Using ISO 27001:
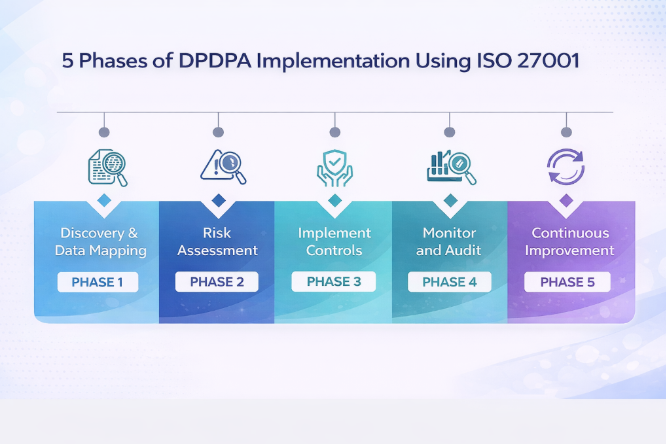
Organizations can use the Plan–Do–Check–Act (PDCA) framework of ISO 27001 to operationalise personal data protection effectively.
Phase 1: Discovery & Scoping (Plan)
Before implementing controls, organizations must understand where personal data exists and how it flows across systems.
Data Mapping
Identify and classify all personal data processed by the organization. This includes documenting:
A comprehensive data map provides visibility into how personal data moves across the organization.
ISMS Scope Definition
Update the ISO 27001 ISMS scope to include systems and processes involved in personal data collection, storage, and processing. This ensures that data protection obligations are integrated into security governance.
Phase 2: Risk Assessment & Control Design (Plan)
Once data visibility is established, organizations must evaluate the risks associated with personal data processing.
Risk Assessment
Conduct a structured risk analysis focusing on threats to:
Both internal and external threats should be considered.
Control Mapping
Map ISO 27001:2022 Annex A controls to DPDPA requirements.
Relevant examples include:
Gap Analysis
Compare existing security controls with DPDPA obligations to identify gaps in areas such as:
Phase 3: Implementation & Operationalisation (Do)
After designing the control framework, organizations must implement operational mechanisms that protect personal data.
Consent Management
Implement systems that capture, track, and manage user consent, including mechanisms to handle consent withdrawal.
Technical Security Controls
Deploy strong technical safeguards such as:
These measures help ensure that only authorized users can access personal data.
Data Lifecycle Management
Establish clear policies governing the lifecycle of personal data, including:
This reduces unnecessary data storage and minimizes compliance risks.
Phase 4: Monitoring & Compliance (Check)
Compliance requires continuous monitoring and validation of implemented controls.
Incident Response and Breach Notification
Organizations must maintain incident response procedures capable of detecting breaches and meeting mandatory notification timelines defined under DPDPA.
Vendor Governance
Third-party vendors handling personal data should be assessed through structured risk evaluation and contractual security obligations.
Internal Audits
Regular internal audits ensure that privacy controls are functioning effectively and align with both ISO 27001 and DPDPA requirements.
Phase 5: Continuous Improvement (Act)
Data protection is an ongoing process that requires regular refinement and improvement.
Employee Training
Organizations should conduct regular training programs to build awareness around privacy responsibilities and secure data handling practices.
Management Review
Leadership should periodically review security metrics, audit findings, and incident reports to improve policies and strengthen the ISMS.
Continuous improvement ensures that the organization’s security posture evolves alongside changing technologies and regulatory expectations.
Moving Beyond Compliance:

When implemented through ISO 27001, DPDPA compliance becomes more than a regulatory obligation.
It becomes a structured data governance and security framework that helps organizations:
For CISOs, the objective is not simply passing audits or maintaining documentation. The real goal is building a sustainable data protection ecosystem that evolves with the organization’s digital infrastructure, vendor relationships, and regulatory expectations.
As businesses adopt more cloud platforms, SaaS tools, and third-party integrations, personal data continues to move across increasingly complex environments. Without structured governance and continuous monitoring, even well-designed policies can lose effectiveness over time.
By aligning DPDPA implementation with ISO 27001’s operational framework, organizations gain the ability to continuously identify risks, validate security controls, and maintain visibility into how personal data is handled across systems.
This shift moves compliance from a reactive exercise to a proactive security capability that strengthens long-term organizational resilience.
A Question Every CISO Should Ask:
Before regulators, partners, or customers ask for proof of compliance, leadership should already have clear answers to critical questions:
Organizations that can answer these questions confidently are not just compliant they are operationally prepared for modern data protection risks.
In the end, “compliance is not defined by policies or frameworks.
It is defined by how effectively organizations protect personal data in real-world operations”.
Frequently Asked Questions:
How does ISO 27001 support DPDPA compliance?
ISO 27001 provides a structured framework for managing information security through policies, risk assessments, and technical controls. Organizations can use this framework to implement governance, monitoring, and protection mechanisms required for DPDPA compliance.
Is ISO 27001 certification mandatory for DPDPA compliance?
No, ISO 27001 certification is not legally required for DPDPA compliance. However, it is widely used because it provides a globally recognized framework for managing information security and protecting personal data.
What are the key steps for implementing DPDPA in an organization?
Key steps include data mapping, risk assessment, consent management, access control implementation, vendor risk management, breach notification procedures, and continuous monitoring of data protection controls.
Why is data mapping important for DPDPA compliance?
Data mapping helps organizations understand where personal data exists, how it flows across systems, and who has access to it. This visibility is essential for protecting personal data and demonstrating regulatory accountability.
.png)