Stryker Cyber Attack: What It Reveals About Modern Cyber Risk in Healthcare
Introduction

Healthcare is no longer just about patient care, it is about data, connectivity, and digital ecosystems.
From connected medical devices to cloud-based patient records and third-party service providers, healthcare organizations today operate in highly interconnected environments. While this transformation improves efficiency and care delivery, it also introduces new layers of cyber risk that are often underestimated.
The Stryker cyber attack is a strong example of this reality.
It wasn’t just a technical incident. It reflected how modern cyber threats exploit complex systems, trusted relationships, and visibility gaps.
In this blog, we break down the Stryker cyber attack, what it reveals about cybersecurity in healthcare, and what organizations must do to stay resilient.
Understanding the Stryker Cyber Attack
Stryker Corporation, one of the world’s leading medical technology companies, faced a cybersecurity incident involving unauthorized access to certain systems. While the company acted quickly to contain the situation and reported no major disruption to its operations, the incident highlighted several important concerns.
These include:
What makes this incident significant is not just what happened—but how it happened.
Like many modern cyber attacks, it was not about breaking through strong defences.
It was about finding and exploiting weak points in a connected ecosystem.
Why This Incident Matters to Every Organization
Many organizations believe cyber attacks happen only when systems are poorly secured.
But most cyber incidents today happen because:
The Stryker cyber attack reinforces a critical shift in cybersecurity thinking:
Risk does not always come from what is broken.
It often comes from what is assumed to be secure.
This is especially true in industries like healthcare, where operational continuity and trust are critical.
The Expanding Attack Surface in Healthcare
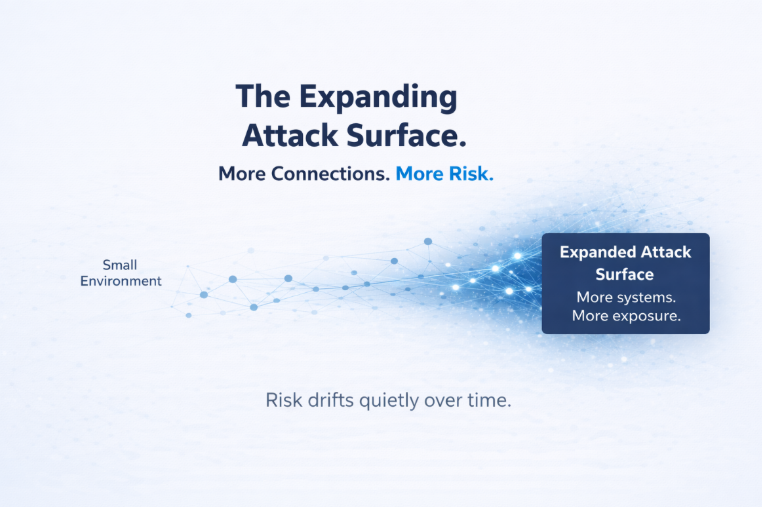
Healthcare organizations today operate across multiple layers:
Each layer introduces new entry points for attackers.
As organizations grow, so does their attack surface—often without full visibility into how systems interact.
For example:
These risks don’t always appear immediately.
They evolve quietly over time.
Key Cybersecurity Risks Highlighted by the Stryker Incident
1. Third-Party and Supply Chain Risk
One of the most critical lessons from the Stryker cyber attack is the importance of managing third-party risk.
Healthcare organizations depend on vendors for:
Each vendor becomes part of the organization’s extended environment.
If a third-party system is compromised, attackers can use it as a pathway into your systems.
This is why supply chain cyber attacks are increasing globally.
Organizations must move beyond basic vendor onboarding and implement:
2. Medical Device Security Challenges
Connected medical devices are essential to modern healthcare but they also present unique cybersecurity challenges.
Many devices:
This makes them difficult to secure.
A compromised device can:
The Stryker cyber attack highlights the need to treat medical devices as critical cybersecurity assets, not just operational tools.
3. Identity and Access Management Gaps
Identity is now the primary entry point for attackers.
Over time, organizations accumulate:
These create hidden vulnerabilities.
Attackers no longer need to “hack” systems, they simply use valid credentials to move across environments.
This is why strong Identity and Access Management (IAM) practices are essential:
4. Lack of Continuous Security Validation
One of the biggest gaps exposed by incidents like Stryker is the reliance on periodic security checks.
Many organizations still depend on:
But real-world environments are dynamic.
Every day:
Without continuous validation, organizations lose visibility into their actual risk posture.
Risk doesn’t spike suddenly.
It drifts over time quietly and unnoticed.
Compliance vs Real Security: A Critical Gap
Healthcare organizations often follow frameworks like:
These frameworks provide structure and guidelines.
But they do not guarantee that systems are secure in real-world conditions.
Compliance ensures:
Security requires:
The Stryker cyber attack clearly demonstrates this gap.
Security proves effectiveness.
Business Impact of Cyber Attacks in Healthcare
Cyber attacks in healthcare are not just technical incidents—they have broader business implications.
1. Financial Impact
2. Reputational Damage
3. Regulatory Consequences
4. Operational Disruption
In extreme cases, cyber incidents can directly affect patient care and safety.
What Organizations Must Do Differently
1. Understand Your True Attack Surface
Most organizations only see part of their environment.
You must identify:
2. Implement Continuous Security Monitoring
Security must be ongoing—not periodic.
This includes:
3. Perform Regular VAPT
Vulnerability Assessment and Penetration Testing (VAPT) help identify real-world weaknesses.
It simulates attacker behaviour and reveals:
4. Strengthen Vendor Risk Management
Treat vendors as part of your attack surface.
Key actions:
5. Prioritize Identity Security
Identity is the new perimeter.
Organizations must:
6. Shift from Reactive to Proactive Security
Waiting for alerts is no longer enough.
Organizations must:
The Bigger Reality: Cyber Risk Is Evolving Faster Than Controls
The Stryker cyber attack reflects a larger trend.
Organizations are:
Attackers, on the other hand, are:
They don’t follow compliance frameworks.
They follow what is reachable.
Final Thoughts
The Stryker cyber attack is not just about one organization.
It reflects how modern cyber risk works.
The most important question today is not:
“Are we compliant?”
The real question is:
“If an attacker looked at our systems today, what would they find first?”
Organizations that continuously ask this and validate their answers build true resilience.
Those that rely only on compliance risk discovering the answer too late.
Frequently Asked Questions (FAQ)
1. What happened in the Stryker cyber-attack?
The Stryker cyber-attack involved unauthorized access to some systems within the company. While there was no major disruption reported, it highlighted how attackers can exploit connected systems and third-party access rather than directly breaking security controls.
2. Why are healthcare organizations easy targets for cyber-attacks?
Healthcare systems are highly connected and store sensitive patient data. With multiple systems, vendors, and devices involved, it becomes difficult to maintain full visibility, making them attractive targets for attackers.
3. What is an attack surface in simple terms?
An attack surface is all the places where an attacker can try to enter a system. This includes servers, cloud systems, apps, devices, and even user accounts.
4. Is compliance enough to keep systems secure?
No. Compliance helps set rules and processes, but it does not guarantee real security. Systems need continuous monitoring and testing to stay secure in real-world conditions.
5. How can companies reduce cyber risk quickly?
Companies can reduce risk by regularly testing their systems (VAPT), limiting access permissions, monitoring systems continuously, and reviewing third-party access.
.png)