Top Open-Source Security Risks in 2026: Why Code Scanning Alone Is Not Enough
Explore top open-source security risks in 2026 and why code scanning alone is not enough. Learn how visibility, access control, and continuous validation reduce cybersecurity exposure. Organizations need better visibility through structured cybersecurity risk assessment to understand real-world exposure.
Open-source software has become the foundation of modern application development. From fast-growing SaaS companies to large enterprises, organizations rely heavily on open-source components to accelerate development, reduce costs, and scale quickly. It enables teams to move faster, innovate rapidly, and build complex systems without beginning from nothing.
But this speed comes with a trade-off.
As organizations increasingly depend on open source, their environments become more interconnected, more dynamic, and significantly harder to fully understand. Most organizations believe they are managing open-source security risks effectively. They run code scans, track vulnerabilities, and follow compliance frameworks. On paper, everything appears secure.
Yet, breaches continue to happen not because security tools are missing, but because the focus is misplaced.
The real issue is not just vulnerable code. It is the lack of visibility into how open-source components behave within real-world environments.
Traditional Open-Source Risk

A few years ago, open-source security was about identifying known vulnerabilities. Security teams focused on patching outdated libraries, tracking CVEs, and maintaining dependency hygiene. This approach worked when systems were simpler and more contained.
Modern Open-Source Risk Landscape
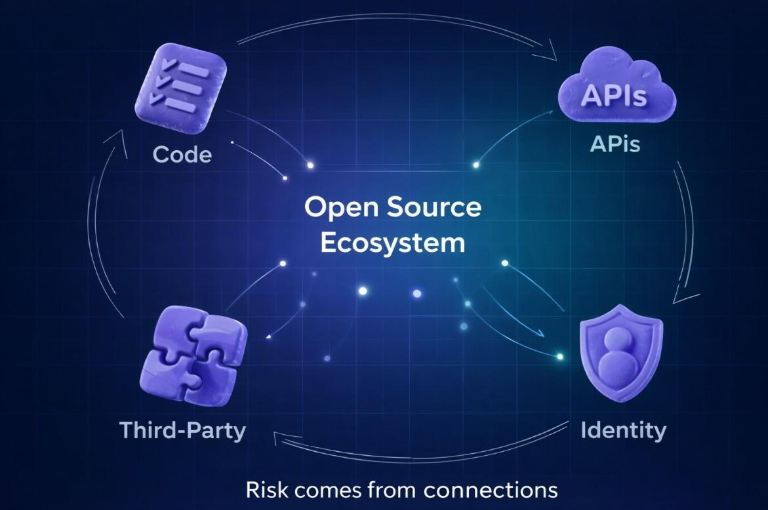
Today, the landscape is quite different. Modern applications are distributed across cloud platforms, built on microservices, and deeply integrated with third-party services. APIs connect systems, identities manage access, and data flows across multiple environments. Open-source components are no longer isolated pieces of code they are part of a broader ecosystem that defines what your systems can access, influence, and expose. It is no longer about what exists in your codebase. It is about what your systems are connected to and what those connections enable.
The Limitation of Code Scanning
Code scanning tools are an essential part of any security program. They help identify known vulnerabilities, outdated dependencies, and potential issues within the code. They provide valuable insights and should remain a foundational control.
However, they operate within a limited scope.
Code scanning answers a static question:
But real-world security is dynamic.
A component with no known vulnerabilities can still introduce significant risk if it has excessive permissions, access to sensitive systems, or trusted connections that are not continuously validated. A fully patched dependency can still be misused if it sits within an over-permissioned environment.
Code scanning tells you the condition of the code.
It does not tell you how that code behaves in production.
This gap between code-level analysis and system-level behaviour is where most organizations are exposed.
Where the Real Risk Exists
Open-source risk rarely originates from the code itself. It emerges from how that code is used within a complex and evolving environment.
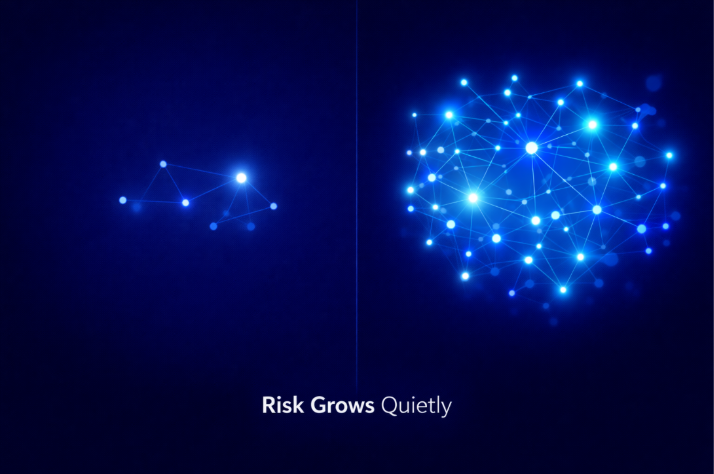
Permissions are often granted once and rarely revisited. Over time, access expands, tokens remain active longer than intended, and components operate with more privilege than necessary. Nothing appears broken, but exposure increases silently.
At the same time, integrations continue to grow. Applications connect with SaaS platforms, payment systems, analytics tools, and internal services. Each integration creates a trusted pathway, but very few organizations continuously validate whether that trust is still justified.
Dependency chains add another layer of complexity. A single library may introduce multiple indirect dependencies, some of which are not actively monitored or even fully understood. Organizations often secure what they can see, while risk accumulates in what they cannot.
All of this is compounded by gradual change. New features, new vendors, and new data flows continuously reshape the system. Security posture shifts over time, but validation does not always keep up. This creates what many organizations fail to detect security drift.
How Attackers Actually Think
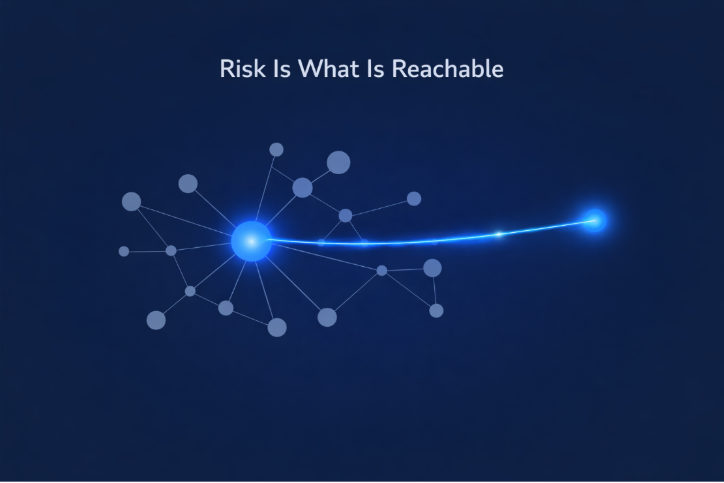
Attackers do not approach systems the way security teams do.
They are not focused on whether your code has vulnerabilities. They are focused on whether your systems provide a path.
Their thinking is simple:
If a path exists, they use it.
They do not need to exploit code if access is already available. This is why many modern breaches do not begin with zero-day vulnerabilities or highly sophisticated techniques. They begin with existing permissions, overlooked integrations, and trusted relationships that were never revalidated.
In many cases, attackers are not breaking systems. They are navigating them.
The Shift Organizations Need to Make

To address these risks, organizations need to move beyond a tool-centric approach to security.
The goal is not just to detect vulnerabilities.
It is to understand and validate real-world exposure.
This begins with visibility. Organizations must understand what their systems are connected to, what data is accessible, and how components interact across environments. Without this visibility, security decisions are based on assumptions rather than evidence.
Security must also become continuous. Environments evolve rapidly, and static assessments cannot keep pace. Ongoing monitoring, regular validation, and periodic reassessment of access are essential to maintaining control.
Finally, security must align with real system behaviour. Policies and documentation are important, but they are only effective if they reflect how systems operate. Controls must be tested under realistic conditions to ensure they work as intended.
Moving Beyond Compliance
Compliance frameworks such as ISO 27001 and NIST provide valuable structure. They help organizations define policies, implement controls, and establish governance. They are essential for building a strong foundation.
But compliance alone does not guarantee security.
It validates that controls exist and processes are documented.
It does not validate that those controls are effective under real-world conditions.
Attackers do not operate within compliance frameworks. They operate within your systems.
Organizations that rely solely on compliance often develop a false sense of security. They meet requirements, pass audits, and maintain documentation. but still lack visibility into actual exposure. Real security begins where compliance ends.
What Strong Open-Source Security Looks Like in 2026
Organizations that effectively manage open-source security risks take a different approach.
They focus on understanding how components interact within the system, not just how they exist in the codebase. They continuously review access, validate integrations, and monitor how data flows across environments.
They treat security as an ongoing process rather than a one-time activity. Instead of assuming controls are working, they test them regularly. Instead of relying solely on tools, they prioritize visibility and validation. Most importantly, they align security with how their systems operate. These organizations do not just assume they are secure. They continuously verify it.
Final Thoughts
Open source is not inherently risky. It is an essential part of modern software development and will continue to play a critical role in innovation.
The real risk lies in assumption assuming that scanned code is secure, that integrations are safe, and that access is still appropriate.
Without continuous validation, these assumptions become blind spots.
And in today’s interconnected environments, blind spots are exactly where attackers focus.
Security is no longer defined by what your code contains.
It is defined by what your systems can reach.
Frequently Asked Questions (FAQs)
What are the biggest open-source security risks in 2026?
The biggest risks include over-permissioned access, hidden dependencies, integration-driven exposure, and lack of visibility into system connectivity.
Why is code scanning not enough?
Code scanning identifies known vulnerabilities but does not evaluate real-world behaviour, access, or how components interact within systems.
How can organizations reduce open-source security risk?
By focusing on continuous validation, access control reviews, real-world testing, and improving visibility across integrations and dependencies.
Is open source insecure?
No. Open source is not inherently insecure. The risk comes from how it is implemented, configured, and connected within systems.
.png)