Why ISO 27001 Is the Missing Pillar in DPDPA Compliance

India’s Digital Personal Data Protection Act (DPDPA) marks a governance shift in data protection compliance in India. The regulatory question is no longer whether personal data is protected. It is whether that protection can be demonstrated under scrutiny.
Many organizations approaching DPDPA compliance in India focus on policies, consent notices, and documentation updates. However, regulators will assess more than written intent. They will evaluate risk assessment discipline, security safeguard effectiveness, breach response maturity, and audit readiness.
This is where ISO 27001 becomes indispensable.
ISO 27001 for data protection establishes a structured Information Security Management System (ISMS) that embeds formal risk assessment methodologies, defined security controls, continuous monitoring, and internal audit mechanisms into the compliance framework. Without this operational backbone, DPDPA implementation remains fragmented and difficult to defend.
For data fiduciaries, ISO 27001 converts regulatory obligation into measurable governance.
The Structural Weakness in Standalone DPDPA Implementation:
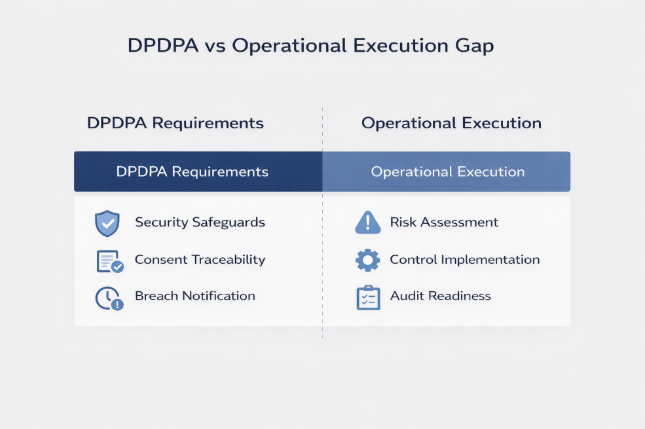
The DPDPA compliance framework requires reasonable security safeguards, traceable consent management, structured risk assessments, and breach notification within defined timelines.
The Act defines obligations. It does not define execution.
Without structured governance, compliance becomes inconsistent. Risk assessments lose rigor. Access control governance weakens. Consent records lack audit defensibility. Documentation fragments across teams. Audit preparedness becomes reactive.
This gap between regulatory expectation and operational execution creates exposure.
DPDPA demands proof.
ISO 27001 institutionalizes proof.
From Legal Alignment to Risk-Based Governance:

ISO 27001 introduces a disciplined, risk-based governance model. Organizations are required to identify risks, assess impact, implement risk treatment plans, and continuously validate control effectiveness.
This strengthens DPDPA risk assessment processes and security safeguard requirements while embedding accountability into operational workflows.
Beyond risk management, ISO 27001 formalizes asset inventories, data classification frameworks, defined ownership structures, access control governance, logging discipline, and documented internal review cycles. Compliance shifts from policy declarations to measurable control maturity.
When regulators assess data protection compliance in India, they evaluate governance strength, not just documentation. ISMS implementation ensures DPDPA compliance is operationally embedded and continuously validated.
Consent Under DPDPA Requires Traceability, Not Visibility:
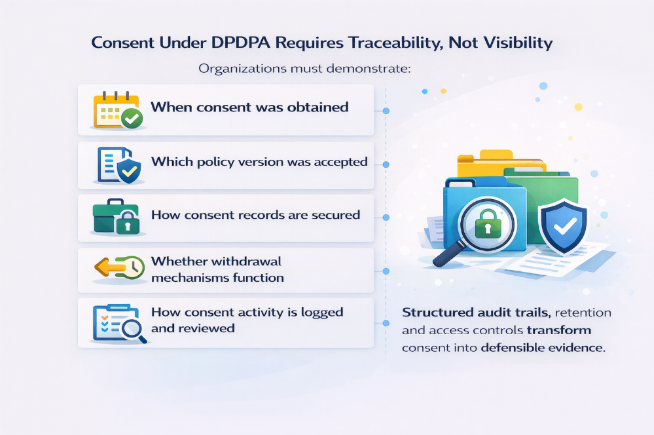
Consent management under DPDPA is frequently treated as a front-end exercise. But regulatory defensibility depends on traceability.
Organizations must demonstrate:
Without structured logging, access governance, and evidence retention controls, consent becomes vulnerable under scrutiny.
ISO 27001 embeds documented controls, audit trails, and monitoring processes within the ISMS, transforming consent from symbolic compliance into defensible evidence.
Incident Governance and Enforcement Readiness:
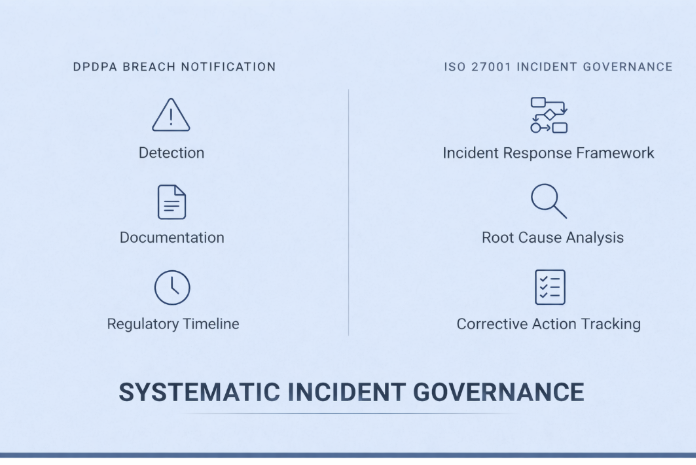
DPDPA breach notification requirements elevate accountability. Organizations must detect, assess, document, and report incidents within regulatory timelines.
ISO 27001 mandates formal incident response frameworks, escalation protocols, root cause analysis, and corrective action tracking. Breach handling becomes systematic, not improvised.
For organizations prioritizing DPDPA audit preparedness, structured incident governance is foundational.
ISO 27001 and DPDPA: Complementary by Design:
DPDPA defines personal data protection obligations and data fiduciary accountability.
ISO 27001 establishes the operating system a structured ISMS built on risk assessment, documented controls, continuous monitoring, and internal audits.
DPDPA defines the obligation.
ISO 27001 defines execution discipline.
Together, they create a defensible DPDPA compliance roadmap grounded in governance maturity rather than documentation alone.
Sustainable Compliance at Scale:
For SaaS companies and high-growth enterprises, DPDPA compliance for startups presents amplified risk. Infrastructure evolves rapidly. Vendor ecosystems expand. Access privileges scale.
Without structured oversight, compliance maturity erodes as growth accelerates.
ISO 27001 introduces review cycles, internal audits, management oversight, and continuous monitoring ensuring compliance remains stable as systems evolve.
Conclusion: From Obligation to Assurance:
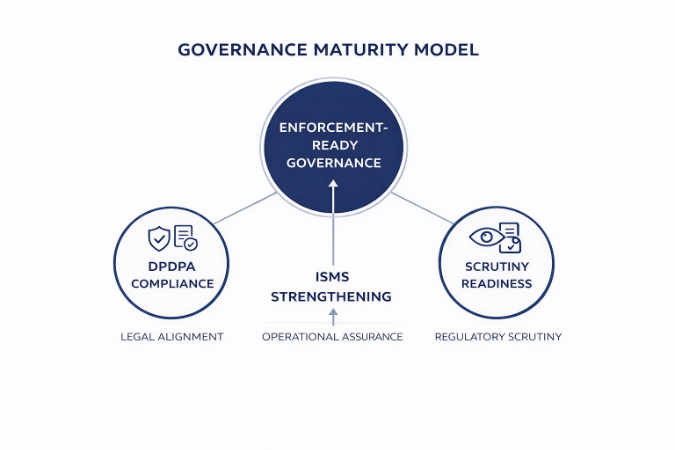
DPDPA has elevated the standard for personal data protection compliance in India. Meeting that standard requires more than legal alignment. It requires structured risk management, enforceable safeguards, and demonstrable governance maturity.
ISO 27001 provides that discipline.
For organizations serious about enforcement-ready, audit-defensible ISO 27001 and DPDPA compliance alignment, ISO 27001 is not a certification milestone.
It is the operational pillar that makes DPDPA compliance credible.
Frequently Asked Questions (FAQ):
1. Is ISO 27001 mandatory for DPDPA compliance in India?
No. ISO 27001 certification is not legally mandatory under the Digital Personal Data Protection Act (DPDPA). However, ISO 27001 provides a structured Information Security Management System (ISMS) that helps organizations implement risk management, access controls, monitoring, and incident response required to demonstrate strong data protection governance under DPDPA.
2. How does ISO 27001 support DPDPA compliance?
ISO 27001 strengthens DPDPA implementation by introducing risk-based security governance, control monitoring, and audit readiness. It helps organizations manage personal data securely through asset management, access control, logging, incident response, and continuous security reviews, making compliance defensible under regulatory scrutiny.
3. What are the biggest challenges organizations face in implementing DPDPA?
Most organizations struggle with data visibility, consent traceability, access governance, and breach response readiness. While policies and documentation may exist, the real challenge is proving that security controls operate effectively across systems, vendors, and cloud environments.
4. Why do companies adopt ISO 27001 while preparing for DPDPA?
Organizations adopt ISO 27001 because it converts regulatory requirements into structured governance practices. It establishes documented controls, internal audits, risk treatment plans, and continuous monitoring, ensuring that DPDPA compliance remains sustainable as systems and data flows evolve.
.png)