Why Manufacturing Is Becoming a Top Target for Cyberattacks in 2026
Manufacturing was once considered a low-priority target in cybersecurity. Unlike financial institutions or healthcare providers, factories were not seen as high-value environments for attackers. They didn’t hold large volumes of personal data or direct financial assets. But that perception has shifted.
In 2026, manufacturing has become one of the most actively targeted sectors. Not because it suddenly became more valuable, but because it became more connected.
What used to be isolated production environments are now deeply integrated digital ecosystems. Systems that control machinery, manage supply chains, track inventory, and connect vendors are no longer separate. They are interconnected, accessible, and increasingly exposed.
And attackers have adapted faster than most organizations. Organizations are increasingly turning to specialized cybersecurity partners like to assess real-world exposure beyond traditional controls.
From Isolated Systems to Connected Ecosystems
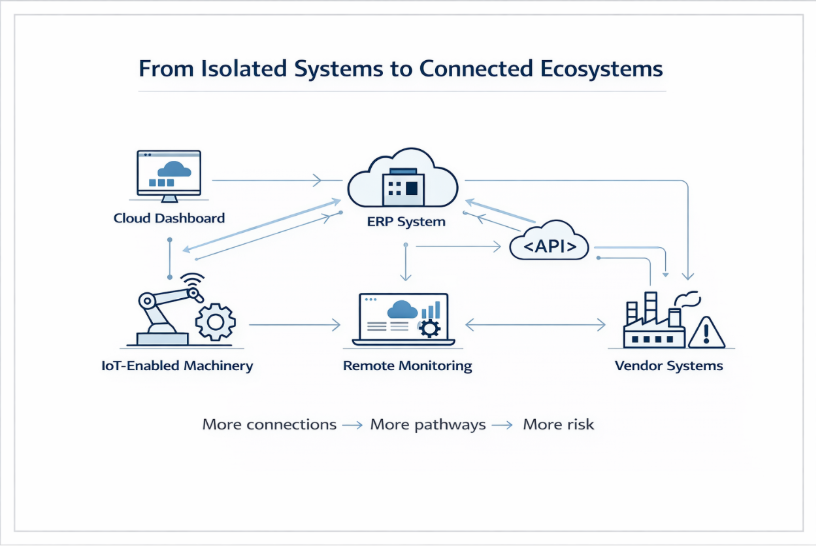
Manufacturing environments have undergone a significant transformation. Traditional Operational Technology (OT) systems, which were once physically separated from IT networks, are now integrated to enable automation, efficiency, and scalability.
Factories today rely on cloud-based ERP systems, IoT-enabled machinery, remote monitoring platforms, and vendor-integrated supply chain tools. These integrations are essential for growth, but they also introduce new forms of access. This is where continuous validation and real-world attack path analysis offered by platforms.
What matters is not just what systems existing, but how they connect.
A machine on the production floor may now communicate with a cloud dashboard. That dashboard may integrate with a vendor system. That vendor system may access internal data through APIs or service accounts. Individually, these connections appear controlled. Together, they create pathways.
And attackers don’t attack systems in isolation. They follow paths.
Why Manufacturing Is Uniquely Vulnerable
Manufacturing environments combine several risk factors that make them highly attractive targets.
There is a strong dependency on uptime. Any disruption directly impacts production, revenue, and delivery commitments. This urgency often forces organizations to respond quickly during incidents, sometimes without fully understanding the impact.
There is also a mix of legacy and modern systems. Many factories still rely on older equipment that was never designed with cybersecurity in mind. These systems are difficult to patch and often remain exposed.
Visibility is another challenge. Security teams typically have strong oversight of IT systems but limited insight into OT environments. This creates blind spots where attackers can operate without detection.
Finally, trust relationships are complex. Vendors, contractors, and third-party platforms often have access to internal systems. These access levels are rarely reassessed over time.
This combination high impact, low visibility, and extended trust create an environment where attacks can succeed quietly.
Integrations: The Real Expansion of Risk
Modern manufacturing depends on integrations. Systems communicate through APIs, tokens, and service accounts to maintain efficiency and coordination.
To avoid operational friction, permissions are often broader than necessary. Access that was intended for a specific purpose gradually expands. Systems begin to trust each other implicitly. Data flows across multiple environments without constant review. Nothing appears broken. Operations continue as expected. But the environment becomes more reachable.
And reachability is what attackers exploit.
A compromised vendor account can provide access to internal dashboards. A misconfigured API can expose production data. A token that was never rotated can become an entry point.
The risk is not in a single vulnerability. It is in how systems interact over time.
Ransomware and Operational Disruption
Ransomware has become one of the most dominant threats in manufacturing. Unlike other industries where data theft is the primary objective, manufacturing attacks often focus on disruption.
Attackers understand that downtime has immediate consequences. When production stops, losses begin instantly. This creates pressure to resolve incidents quickly.
Ransomware in manufacturing often involves shutting down production systems, encrypting operational data, and disrupting supply chain processes. By the time the attack is triggered, attackers may have already moved across multiple systems.
The impact is not limited to IT systems. It affects operations, logistics, and business continuity.
Real-World Example: Supply Chain Impact at Scale
A widely cited example of this risk is the cyberattack involving a supplier connected to Toyota.
The attack targeted a supplier responsible for manufacturing critical components. As a result, the supplier was forced to halt operations. This disruption cascaded across the supply chain, forcing Toyota to stop production across multiple plants. The attack was not aimed at Toyota directly. It targeted a weaker link within the ecosystem.
But because modern manufacturing environments are interconnected, the impact extended far beyond the initial breach.
This highlights a critical reality. Manufacturing risk is not confined to internal systems. It extends across every connected entity.
Supply Chain as the New Attack Surface
Manufacturing supply chains involve multiple vendors, partners, and service providers. Each connection introduces a potential entry point.
Security is often evaluated at the organizational level. But attackers exploit relationships. A smaller vendor with limited security controls can become the entry point into a larger network. Once inside, attackers can move across systems, leveraging trust relationships.
This is why supply chain attacks are increasing. They allow attackers to bypass strong defences by targeting weaker links. Identifying these hidden entry points across vendor ecosystems requires deeper visibility into interconnected systems, not just isolated security checks
Why Traditional Security Approaches Fall Short
Most organizations have invested in security tools and compliance frameworks. They conduct vulnerability scans, implement access controls, and follow established standards. These approaches are necessary, but they are not sufficient. They focus on individual systems. They validate configurations. They ensure policies are followed.
But they do not capture how systems behave together.
They do not answer:
This is where modern attacks operate.
Attackers don’t look for isolated weaknesses. They look for sequences paths that allow movement from one system to another.
The Rise of Smart Factories and Evolving Risk
As manufacturing moves toward Industry 4.0, smart factories are introducing a new layer of complexity.
Automation, AI-driven systems, and real-time analytics platforms are now embedded into production environments. Machines are no longer just executing instructions. They are responding to data, adapting to conditions, and interacting with multiple systems.
This creates dynamic environments where system behaviour changes continuously. While this improves efficiency, it also increases unpredictability. A compromised data input can influence machine behaviour. A manipulated sensor can alter production decisions. And because systems are interconnected, the impact can spread quickly. Traditional security models were not designed for environments where systems evolve in real time. This makes validation critical not just of controls, but of behaviour.
The Growing Need for Visibility
The biggest challenge in manufacturing cybersecurity today is visibility.
Organizations need to understand how systems are connected, where trust relationships exist, and what paths an attacker can take.
Without this visibility, security becomes reactive. You discover issues only after they are exploited. Manufacturing environments require a shift in approach one that focuses on mapping relationships and validating interactions between systems. Because risk is not defined by what exists. It is defined by what is reachable.
What Needs to Change
To address these challenges, organizations need to rethink how they approach security. This does not mean abandoning existing controls. It means extending beyond them. The focus needs to shift from individual systems to interconnected environments, from static configurations to dynamic behaviour, and from assumed security to validated security. This involves understanding how systems interact, continuously validating access paths, and testing environments under real-world conditions.
The question is no longer “Are we secure?”
It is “If someone gets in, what can they reach?”
Leadership Perspective: Cyber Risk Is Operational Risk
Cybersecurity in manufacturing is no longer just a technical issue. It is an operational and business risk.
A single incident can stop production, disrupt supply chains, and impact revenue. It can affect customer commitments and long-term trust. This makes cybersecurity a leadership concern. Decisions should not be based only on compliance status or tool deployment. They should be based on real-world exposure.
Because risk is not defined by what is documented. It is defined by what is reachable. Organizations that actively validate their security posture through real-world testing and exposure analysis rather than relying solely on compliance are better positioned to manage modern cyber risk.
Conclusion
Manufacturing has become a top target for cyberattacks not because it is inherently weak, but because it is deeply connected.
Integrations have expanded access. Trust relationships have grown complex. Systems that were once isolated are now part of larger ecosystems. This creates environments where attackers can move silently, leveraging connections rather than breaking defences.
Cyberattacks fail because a single system fails. They succeed because multiple systems work together in ways no one fully understands. And until that visibility improves, manufacturing will remain one of the most attractive targets.
Frequently Asked Questions
1.What makes manufacturing a top target for cyberattacks in 2026?
Manufacturing environments are highly connected, rely on uptime, and involve complex supply chains, making them attractive for disruption-focused attacks like ransomware.
2.How do cyberattacks impact manufacturing operations?
They can halt production, disrupt supply chains, cause financial losses, and impact delivery commitments.
3.Why are supply chain attacks increasing in manufacturing?
Attackers target smaller vendors with weaker security controls to gain access to larger manufacturing networks.
4.What is the biggest cybersecurity challenge in manufacturing today?
Lack of visibility into how interconnected systems behave and how attackers can move across them.
.png)