Why Penetration Testing Is No Longer Optional: The Hidden Risk Most Businesses Still Miss
Introduction

Most companies don’t ignore security. They invest in it, implement tools, follow frameworks, and build processes that are meant to protect their systems. For a while, everything feels stable and under control.
But the system you secured a few months ago is rarely the same system you’re running today.
New integrations get added to support growth. Access is extended to teams and vendors. Data begins to move across more systems than originally planned. None of this looks risky on its own, and nothing immediately breaks. There are no alerts, no visible failures, and no reason to question the setup.
Yet something important changes quietly in the background. Your environment becomes more connected, more dependent on trust, and ultimately more reachable than before.
That shift is subtle, but it changes how your system behaves under pressure.
And more importantly, it changes how an attacker sees your environment.
The Problem Isn’t Lack of Security

If you speak to most teams, they’ll tell you with confidence that security is already in place. Policies are defined, access controls are configured, compliance requirements are met, and tools are actively running.
From a checklist perspective, everything looks solid.
The issue is not that security is missing. It’s that security is assumed to remain effective even as the environment evolves. Systems change faster than they are revalidated, and over time, the original assumptions about security stop reflecting reality.
In many cases, teams continue to operate based on how the system was designed not how it currently behaves.
That difference may seem small, but it creates blind spots.
And blind spots are where attackers focus.
How Risk Actually Builds Over Time
Risk rarely appears as a single, obvious issue. It builds gradually through small, everyday changes that seem harmless in isolation.
A new API is introduced to support a feature. A third-party vendor is given access to speed up operations. A SaaS tool is connected to internal systems. Permissions are expanded slightly to avoid friction during development or deployment.
Each of these decisions makes sense at the time. They help the business move faster.
But over time, they accumulate.
The system becomes more interconnected. Dependencies increase. Trust relationships expand between components that were never originally designed to work together at this scale.
And because each change is small, no one steps back to reassess the full picture.
That’s the real problem.
Risk doesn’t spike suddenly.
It drifts.
What Changes That Most Teams Don’t Track
As environments evolve, certain shifts happen quietly in the background, and these are rarely tracked properly.
Access permissions tend to expand but are rarely reduced. What starts as temporary access often becomes permanent. Over time, users, services, and integrations hold more privileges than they need.
Data flow also becomes more complex. Information that once stayed within a single system begins to move across logs, analytics tools, third-party platforms, and internal dashboards. Each movement increases exposure, but these flows are rarely mapped end-to-end.
Integrations add another layer of complexity. New tools are connected to improve efficiency, but older integrations are rarely reviewed. Many continue to operate with outdated permissions or unused access tokens.
At the same time, internal systems begin to trust each other more deeply. This makes operations smoother, but it also creates pathways that can be exploited if one system is compromised.
Individually, none of these changes seem critical.
Together, they redefine your attack surface.
Why Compliance Doesn’t Reveal This Risk

Compliance frameworks play an important role. They bring structure, accountability, and consistency to how organizations manage security. When audits are passed and controls are documented, it creates a strong sense of confidence.
But compliance operates within boundaries.
It validates what has been defined, not necessarily how systems behave after continuous change. It checks whether policies exist and controls are in place, but it does not always capture how access has evolved, how integrations interact, or how data flows across systems today.
This creates a subtle but critical disconnect.
An organization can be fully compliant and still be exposed, simply because exposure is not defined by documentation. It is defined by what is reachable in the environment.
And reachability changes far more often than compliance are reviewed.
What Penetration Testing Really Changes
Penetration testing shifts the perspective from assumption to reality.
Instead of asking whether controls exist, it focuses on what can be accessed, exploited, or moved across at a given point in time. It approaches the system the way an attacker would not by reviewing policies, but by exploring possibilities.
A pen test doesn’t just identify isolated vulnerabilities. It looks at how different components interact, how trust relationships can be leveraged, and how far access can extend once an entry point is found.
It answers questions most organizations don’t usually ask:
That’s what makes penetration testing different from automated tools.
It connects the dots between systems, not just the issues within them.
What Organizations Usually Discover
What’s interesting is that most pen tests don’t uncover completely unknown, high-severity flaws in isolation. Instead, they reveal combinations of small gaps that, together, create real exposure.
Access is often broader than necessary because it was never reduced after being granted. Internal systems trust each other more than they should, which allows movement once one layer is compromised.
Integrations that were added months ago continue to operate with the same permissions, even though no one has reviewed them since. These integrations often become silent entry points.
Data also tends to travel further than expected. It moves through logs, dashboards, analytics tools, and third-party platforms, creating multiple points of exposure that are rarely tracked end-to-end.
In cloud environments, configurations change frequently. A small misconfiguration on its own may not be critical, but when combined with excessive permissions or exposed services, it can create a clear attack path.
None of these issues stand out individually.
But together, they form pathways that attackers can use.
Rethinking When to Perform Penetration Testing
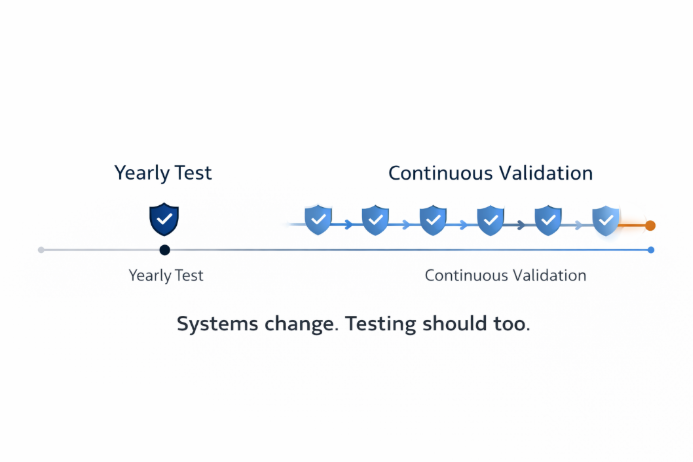
That approach no longer reflects how modern environments operate.
Systems today evolve continuously. New features are released, integrations are added, infrastructure changes are made, and external dependencies grow over time. Testing once a year only captures a snapshot, not the current state.
A more practical way to think about it is this:
If your environment changes frequently, your validation should too.
This doesn’t always mean constant testing, but it does mean testing at meaningful points after major releases, new integrations, infrastructure changes, or when onboarding external vendors.
Because security is not static, and testing shouldn’t be either.
The Shift That Matters
The real shift is not technical. It’s conceptual.
Security cannot be treated as something that is implemented once and then maintained indefinitely. It needs to be continuously validated against how systems behave.
Instead of relying on statements like “we believe it’s secure,” organizations need to ask:
“Have we tested how it behaves today?”
That question changes how decisions are made.
It moves security from assumption to evidence.
Where Most Teams Go Wrong
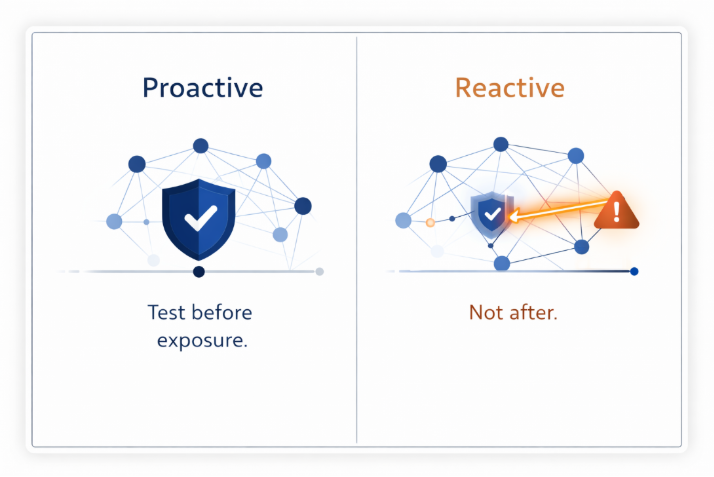
Not because they ignore pen testing.
But because they delay it.
It usually happens after a compliance requirement, a client request, or worse, an incident. By that time, the system has already evolved far beyond what was originally secured.
Risk has already accumulated, and visibility is already reduced.
Penetration testing is most valuable when used proactively before assumptions turn into exposure.
Final Thoughts
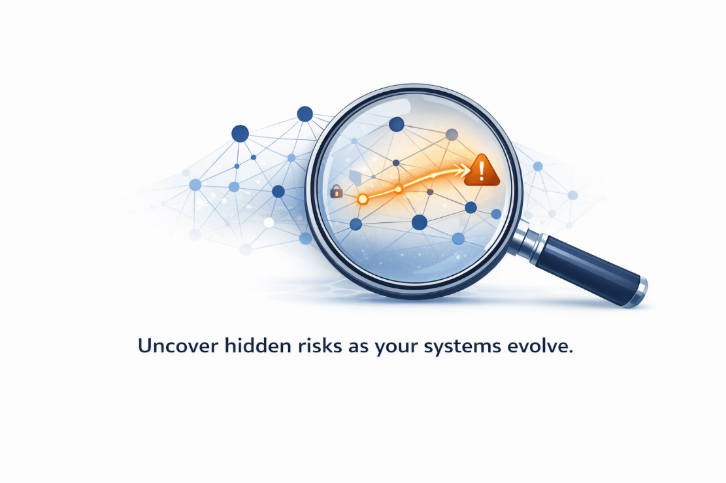
Penetration testing is often viewed as a technical activity focused on identifying vulnerabilities. But its real value lies in something much broader.
It provides a way to step back and understand what your system has become over time.
Because systems don’t just grow, they evolve in ways that aren’t always visible. Connections increase, dependencies deepen, and exposure expands quietly.
And in cybersecurity, those unseen changes are often where the real risk exists.
Closing Line
Penetration testing isn’t about finding vulnerabilities.
It’s about understanding what your systems have quietly become reachable to.
🔍 Frequently Asked Questions (FAQs)
1. What is penetration testing and why is it important for businesses?
Penetration testing is a simulated cyberattack performed on systems, applications, or networks to identify real-world security weaknesses. It is important because it reveals how attackers can exploit your environment, not just what vulnerabilities exist on paper. As systems evolve with integrations and access changes, penetration testing helps validate whether your security controls are still effective.
2. How often should penetration testing be performed?
Penetration testing should not be limited to a yearly exercise. It should be performed after major changes such as new feature releases, system integrations, infrastructure updates, or onboarding third-party vendors. Since modern environments change frequently, testing should align with those changes to accurately reflect current risk exposure.
3. What is the difference between vulnerability scanning and penetration testing?
Vulnerability scanning is an automated process that identifies known security issues based on predefined signatures. Penetration testing goes deeper by simulating real attack scenarios to understand how vulnerabilities can be chained together and exploited. While scanning shows what exists, penetration testing shows what is exploitable.
4. Can a company be compliant and still be vulnerable to cyberattacks?
Yes, a company can be fully compliant and still be exposed to risk. Compliance frameworks validate policies and controls at a point in time, but they do not always reflect how systems behave after continuous changes. As integrations grow and access evolves, hidden attack paths can emerge, making continuous validation through penetration testing essential.
.png)