Your Security Stack Isn’t Broken. It’s Just Not Tested: The Hidden Gaps in App, Mobile, and Cloud Security
Most organizations believe their security is working.
Controls are implemented, tools are deployed, and audits are cleared. There are dashboards showing activity, alerts that appear manageable, and reports that confirm everything is in place. From a leadership perspective, it creates a sense of stability. The environment looks controlled, structured, and protected. But this confidence is often built on a quiet assumption that what has been implemented is working the way it is expected to. The reality is more subtle. The problem most organizations face today is not that their security is broken. It’s that their security has never been tested in the way real-world attackers operate.
Security Doesn’t Break. It Drifts.
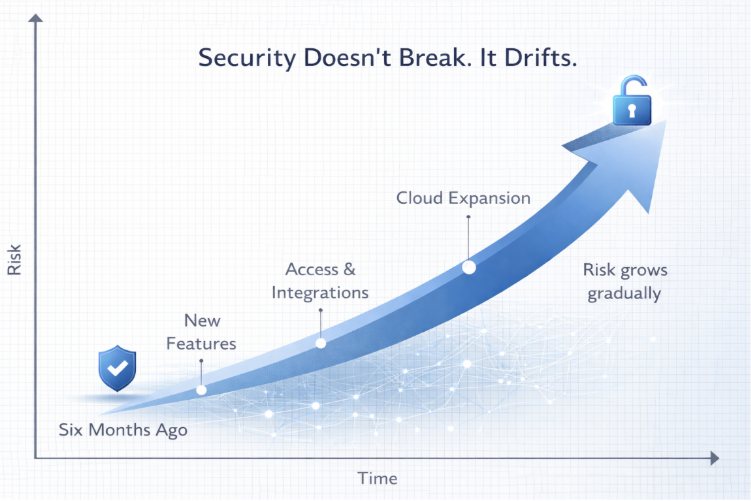
Security failures rarely happen overnight. They don’t appear suddenly as a complete breakdown of systems. Instead, they emerge gradually as environments evolve.
Applications are updated to support new business requirements. Mobile platforms introduce new features and integrations. Cloud environments expand to handle scale, performance, and distributed workloads. Third-party tools are added to improve efficiency. Access is extended across teams, vendors, and services to enable collaboration. Each of these changes is intentional. Each one is justified. And individually, none of them appear risky. But collectively, they reshape the environment.
The system you secured six months ago is no longer the same system you are running today. It has more connections, more dependencies, and more pathways than before. Not weaker in design, but significantly more complex in behaviour. This is where security begins to drift. Not because controls are removed, but because the context in which those controls operate has changed. Permissions that were once appropriate may now be excessive. Integrations that were once isolated may now be interconnected. Data flows that were once simple may now span multiple systems. Nothing is visibly broken. But the environment has become more reachable. And reachability is what defines modern risk.
The Gap Isn’t in Controls. It’s in Connectivity.
Most security programs are built around implementing controls. Organizations invest in access management, encryption, monitoring, endpoint protection, and policy enforcement. These controls are essential, and when evaluated individually, they often perform exactly as expected.
However, security risks rarely exist within individual controls. They emerge in how these controls interact with each other.
A permission that appears reasonable in one system can become risky when combined with access in another. An API that is secure on its own can expose sensitive data when accessed through a trusted integration. A mobile application that stores minimal data can still act as a gateway into backend systems if communication channels are not properly secured.
These are not failures of individual components. They are consequences of connectivity.
As systems become more interconnected, they create pathways that extend beyond what was originally intended. These pathways are not always visible in architecture diagrams or monitoring tools. They exist in the relationships between systems, services, and identities.
And this is where most hidden risks reside.
Attackers Don’t Break Systems. They Traverse Them.
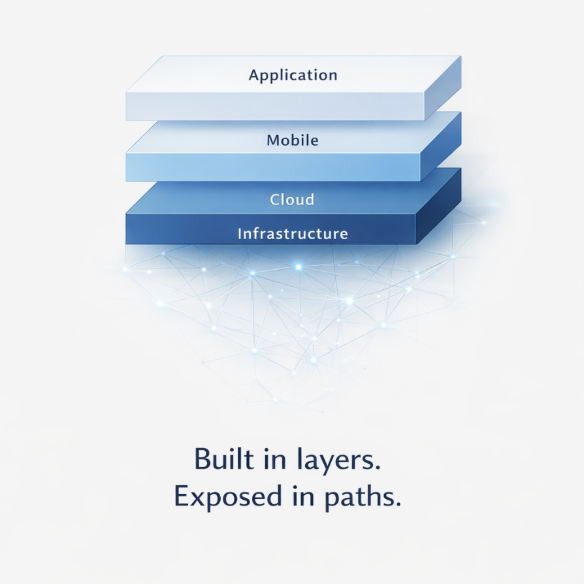
There is a fundamental difference between how organizations design security and how attackers approach it. Security is implemented in layers. Attackers operate across those layers. They don’t begin with the most critical system. They start with what is accessible. A low-privileged account, a public-facing endpoint, or a seemingly minor misconfiguration is often enough.
From there, they move.
They explore how one access point leads to another. They identify trust relationships between systems. They test how permissions can be leveraged in unintended ways. They follow the path of least resistance, not the path of highest impact.
A mobile application may provide an entry point into backend APIs. An API may expose access to cloud resources. A cloud misconfiguration may allow access to sensitive data. Each step is small. Often unremarkable on its own. But together, they form a path. And that path is what enables real-world attacks. Most of these paths do not trigger alerts. They do not violate predefined rules. They simply exist within the environment, waiting to be discovered.
Why Compliance Doesn’t Catch This
Frameworks like ISO 27001 and regulations such as DPDPA play a critical role in modern security programs. They provide structure, define responsibilities, and ensure that organizations implement necessary controls. They establish governance and bring accountability to how data and systems are managed. But compliance has a limitation. It validates what is documented. It confirms that policies exist, controls are implemented, and processes are followed. It ensures that organizations meet defined requirements at a specific point in time. What it does not do is validate how systems behave after continuous change. It does not test how integrations evolve. It does not evaluate how access expands over time. It does not simulate how an attacker would move across systems. As a result, it is entirely possible to be compliant and still have exposure. Because compliance focuses on structure. Real-world risk emerges from behaviour.
Testing Is Not a Checkpoint. It’s Visibility.
This is where testing changes the conversation. Testing shifts the focus from implementation to behaviour. Instead of asking whether a control exists, it asks how that control performs when it is actively challenged. This distinction is critical. Because for most organizations, testing is treated as a periodic activity. Something that is done annually, or before an audit, or to meet a requirement. It becomes a checkpoint rather than a continuous process. But real security testing is not about passing a test.
It is about gaining visibility. In application security testing, this means understanding how business logic, authentication mechanisms, and APIs behave under manipulation. It reveals whether assumptions made during development hold true under real conditions. In mobile security testing, it means analysing how data is stored and transmitted on actual devices, how secure communication channels are, and whether protections can be bypassed by an attacker with physical or logical access. In cloud security testing, it involves evaluating how identities, permissions, and services interact across environments, and whether those interactions create unintended access paths. Individually, these tests provide valuable insights.
Together, they reveal something far more important how your entire environment behaves as a connected system.
The Real Risk Is Not Vulnerabilities. It’s Paths.
Most security efforts focus on identifying vulnerabilities. High, medium, or low severity findings are documented, prioritized, and remediated. This approach is necessary, but it does not fully capture how breaches occur. Because vulnerabilities alone do not define risk. Paths do. A low-severity issue in one system may not be critical. A minor misconfiguration may not raise concern. A trusted integration may appear safe. But when these elements connect, they can create a direct route to sensitive systems.
This is why many real-world incidents do not begin with a single high-risk vulnerability. They begin with multiple small gaps that, when combined, form a viable attack path. Without testing these connections, organizations remain unaware of how far an attacker could go.
Rethinking Security: From Control to Behaviour
To address this gap, organizations need to shift how they define security.
Security is often measured by what is implemented the number of tools deployed, the controls configured, the policies enforced. But real security is defined by behaviour. It is defined by what remains reachable despite those controls. This requires moving from a mindset of implementation to one of validation. Instead of asking whether the right controls are in place, organizations need to understand how those controls perform together under real-world conditions. This is not a one-time effort. It requires continuous validation. Because environments are constantly evolving. Every new feature, every integration, and every change in access introduces the possibility of new exposure. Without ongoing testing, these changes accumulate into unseen risk.
Final Thought
Most security stacks are not broken. They are simply untested in the ways that matter.
And untested systems don’t fail loudly. They fail silently, through assumptions that go unchallenged. In modern environments where applications, mobile platforms, and cloud systems are deeply interconnected, security is no longer defined by what you deploy. It is defined by what your environment allows. Because attackers don’t need to break your system. They only need to understand it better than you do. If you want to understand how your systems behave under real-world conditions, explore our approach to security assessment
Frequently Asked Questions (FAQs)
1. What is penetration testing and why is it important for cybersecurity?
Penetration testing is a security assessment where ethical hackers simulate real-world attacks to identify vulnerabilities in applications, mobile systems, and cloud environments. It is important because it reveals how attackers can exploit weaknesses and move across systems, helping organizations fix issues before they are exploited.
2. How is penetration testing different from vulnerability scanning?
Vulnerability scanning is automated and identifies known issues based on predefined signatures. Penetration testing goes deeper by manually testing how vulnerabilities can be exploited and combined to create real attack paths. It focuses on how systems behave, not just what issues exist.
3. What are the most common cloud security risks organizations face?
Common cloud security risks include misconfigured storage, overly permissive identity and access roles, insecure APIs, lack of visibility into data flows, and weak monitoring of cloud activities. These risks often arise due to rapid cloud adoption and complex integrations.
4. What are the key security risks in mobile applications?
Mobile applications commonly face risks such as insecure data storage, weak authentication, improper session handling, lack of encryption, and vulnerabilities in APIs. Attackers can exploit these to access sensitive user data or backend systems.
5. Why are APIs considered a major security risk in modern applications?
APIs act as bridges between systems and expose critical functionality. If not properly secured, they can allow unauthorized access, data leakage, or privilege escalation. Since APIs are widely used in mobile and cloud environments, they are a common entry point for attackers.
.png)